Programmable Privacy as Web3 Infrastructure: Developer Opportunities on Midnight Network
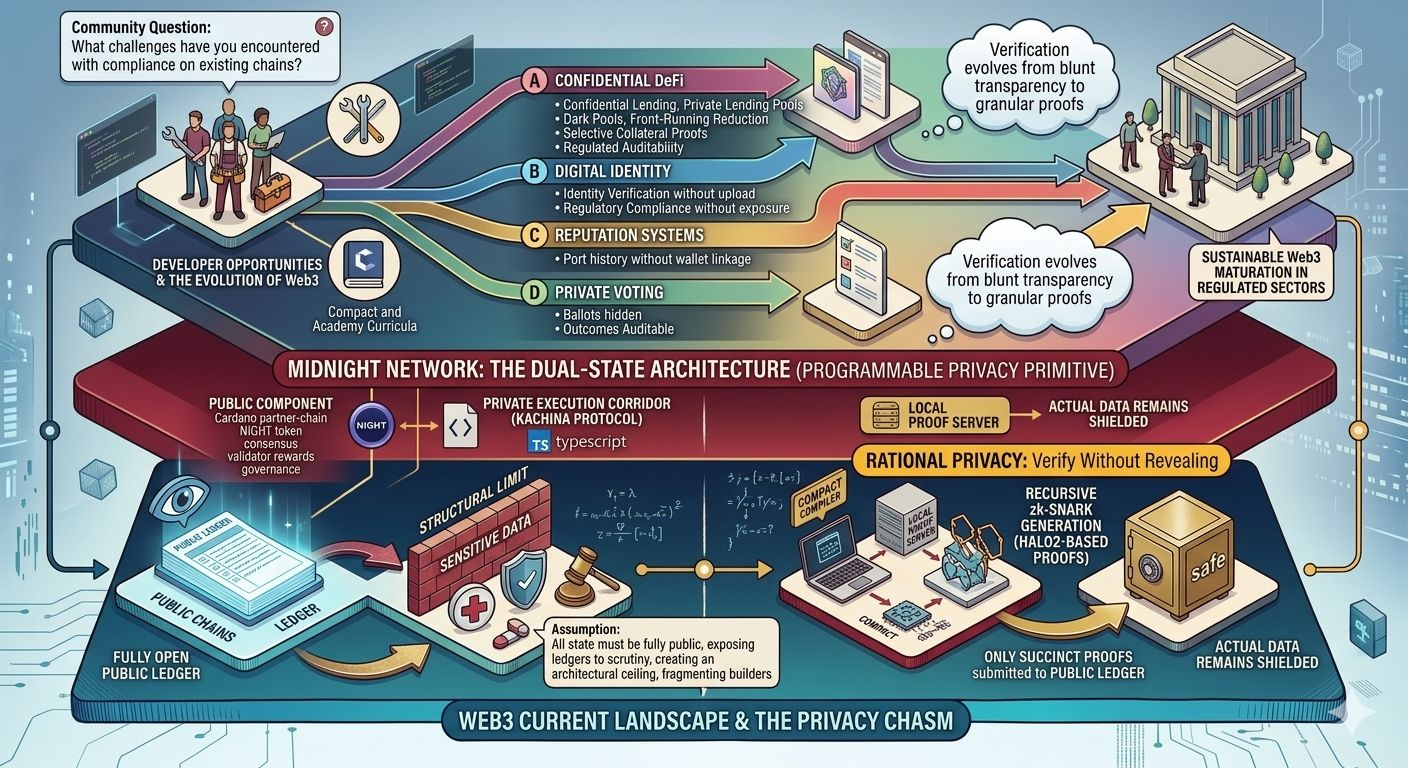
In the rush toward decentralized applications, one persistent structural challenge has quietly limited blockchain’s reach into everyday utility: the assumption that every transaction and state must remain fully public to achieve verifiable trust. Early networks delivered transparency as a virtue, exposing ledgers to scrutiny that built confidence among participants. Yet as developers attempt to move sensitive domains—financial positions, personal credentials, or institutional workflows—onto chain, that same openness becomes a liability. Regulatory regimes demand proof of compliance without wholesale data exposure, users expect control over their information, and counterparties require assurance without surveillance. The result is a quiet fragmentation: builders either accept compromised privacy, rely on centralized intermediaries, or confine innovation to narrow niches. This gap between verifiable systems and confidential ones represents not a temporary inconvenience but an architectural ceiling that has slowed Web3’s maturation beyond speculative layers.
The broader industry has been converging toward this realization for years. Bitcoin established immutable money without intermediaries; Ethereum introduced programmable logic at the cost of total visibility; later generations pursued scalability through zero-knowledge rollups and sidechains. Privacy-focused projects historically leaned toward full anonymity, which complicated compliance and limited institutional interest. Meanwhile, rising data-protection laws and the integration of blockchain into regulated sectors have heightened the need for selective disclosure—mechanisms that prove a statement is true without revealing the underlying facts. Discussions in developer forums and research circles increasingly highlight how public-state architectures force trade-offs that hinder real-world adoption. What has been overlooked is the potential for a dedicated infrastructure layer where privacy is not an add-on but a programmable primitive, enabling applications that maintain verifiability while respecting data sovereignty. Midnight Network positions itself at this inflection point, offering a partner-chain model anchored to established ecosystems like Cardano, where confidential computation can coexist with public settlement.
At its core, Midnight introduces a dual-state architecture that separates public verifiability from private execution. Public components handle consensus, validator rewards, and governance through the native NIGHT token, while private state transitions occur off-chain via the Kachina protocol. Developers write smart contracts in Compact—a domain-specific language built on TypeScript syntax—that define logic for confidential data without requiring deep cryptographic expertise. When a contract processes private inputs, the local proof server generates recursive zk-SNARKs (specifically Halo2-based proofs) that attest to the validity of the transition. Only these succinct proofs are submitted to the public ledger; the actual data remains shielded. This design enables rational privacy: users and applications decide programmatically what to reveal, to whom, and under what conditions. A developer building a confidential lending protocol, for instance, can allow a borrower to prove sufficient collateral without disclosing exact holdings, or an identity system to verify regulatory compliance without uploading personal records.
The structural uniqueness lies in how Midnight embeds verification mechanisms directly into the contract layer. Unlike general-purpose chains where privacy requires custom zero-knowledge circuits written from scratch, Compact abstracts much of the complexity, letting engineers focus on business logic while the network handles proof generation and state separation. Proof servers run locally, ensuring that sensitive computation never leaves the user’s environment, yet the resulting proofs integrate seamlessly with the shared ledger for consensus. This addresses a longstanding developer pain point: the steep learning curve of cryptography that has gated participation in privacy-preserving development. By lowering that barrier and providing tools such as testnet faucets, open-source repositories, and structured academy curricula, Midnight shifts the focus from infrastructure plumbing to application creativity. Early experiments already demonstrate practical patterns—private voting where ballots stay hidden yet outcomes remain auditable, reputation systems that port history across applications without wallet linkage, and credential verification that satisfies auditors without permanent on-chain exposure.
The implications extend beyond individual dApps into the fabric of decentralized finance and trust infrastructure. In DeFi, confidential applications could unlock dark-pool trading, private lending pools, and selective collateral proofs, reducing front-running risks while preserving regulatory auditability. Institutional participants, long wary of public ledgers, gain pathways to on-chain activity without exposing strategies or positions. Broader ecosystem sustainability benefits as well: by enabling compliance-friendly designs, such networks reduce reliance on off-chain custodians and foster genuine decentralization in sectors previously excluded. Verification mechanisms evolve from blunt transparency to granular proofs, strengthening overall trust without eroding user agency. Over time, this infrastructure could support hybrid models where public chains handle settlement and privacy layers manage sensitive logic, creating composable systems that scale responsibly.
Looking ahead, the introduction of programmable privacy layers like Midnight suggests a deeper evolution in Web3 architecture. Rather than treating confidentiality as a specialized feature for niche coins, it becomes foundational infrastructure that allows decentralized systems to mature into regulated environments without losing their core advantages. The next phase of innovation may hinge less on raw throughput or token mechanics and more on how effectively networks reconcile verifiability with data control. Developers who engage with these tools today are not merely building isolated applications; they are shaping the protocols that will determine whether blockchain infrastructure can support the complex, privacy-sensitive workflows of tomorrow’s digital economy. In that sense, the real opportunity lies in reimagining decentralized systems as environments where trust and discretion coexist by design.
Community Question:
What challenges have you encountered when attempting to build confidential or compliance-sensitive applications on existing blockchains, and how might a programmable privacy layer like Midnight influence the types of decentralized tools developers prioritize in the coming years?