The assumption behind most digital systems is simple.
If a network needs to verify something, it must first receive the information that proves it.
A university diploma gets uploaded to confirm education.
A financial document gets submitted to verify collateral.
A medical record gets shared to prove eligibility.
The verification process always begins the same way.
Send the file.
Blockchain did not really change this pattern. It only made the process more transparent. Instead of information sitting inside a company database, transactions moved onto a public ledger visible to every node maintaining consensus.
Transparency solved one problem.
It created another.
The more valuable the data becomes, the less comfortable organizations become placing it on open infrastructure. Healthcare providers cannot expose patient records. Financial institutions cannot broadcast balance sheets. Identity systems cannot publish the documents they are supposed to protect.
Verification works.
Privacy disappears.
This tension sits at the center of modern Web3 architecture.
The network needs enough information to confirm that something happened correctly. But the moment sensitive data enters the ledger, the system begins violating the very confidentiality that real-world applications require.
This is the contradiction **Midnight Network attempts to resolve.
Most blockchains treat all contract inputs the same way.
If a smart contract needs the data, the data must be submitted to the chain. Nodes process it, verify it, and permanently record the result inside the ledger’s history.
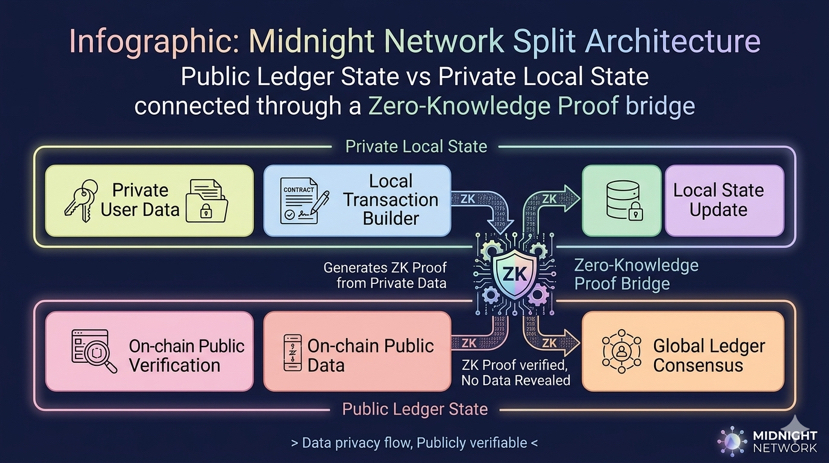
Midnight takes a different approach.
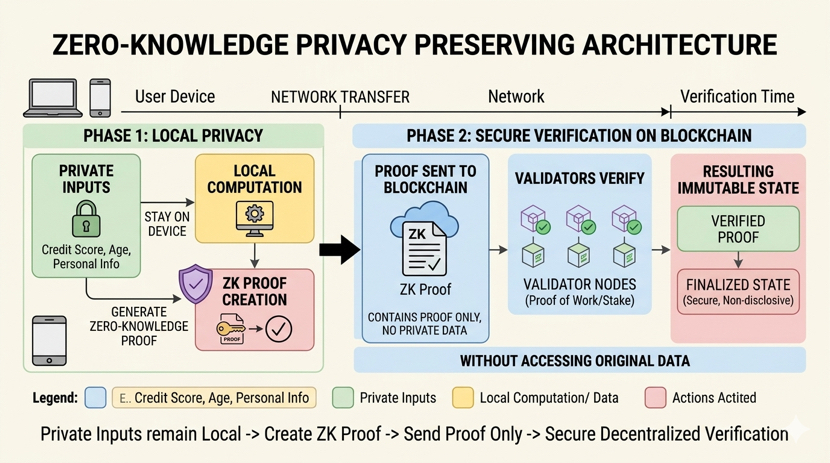
Instead of forcing data into the network, it separates contract execution into two layers.
Public state remains visible to the blockchain and participates in consensus. Private state stays local to the participants interacting with the application. When a transaction occurs, the computation involving sensitive information happens outside the chain entirely.
The network never receives the original data.
What it receives instead is a mathematical proof generated through
Zero-Knowledge Proof systems.
That proof confirms the computation followed the contract’s rules without revealing the inputs used to produce the result.
At first glance the distinction seems subtle.
In practice it changes the behavior of decentralized applications completely.
Imagine an identity verification system built for financial services. A user must prove they are above a certain age, reside in a specific jurisdiction, and pass a regulatory screening process. Traditional blockchain infrastructure struggles with this scenario because the verification data contains personal information that cannot simply be exposed to every validator node.
Midnight shifts where the verification happens.
The identity data stays with the user or the institution managing it. The verification logic executes locally. When the process completes, the system produces a proof that the requirements were satisfied.
The blockchain validates the proof.
The personal records never appear on-chain.
The ledger receives confirmation that the rule passed, but the identity documents themselves remain exactly where they started.
Private.
Controlled.
Unpublished.
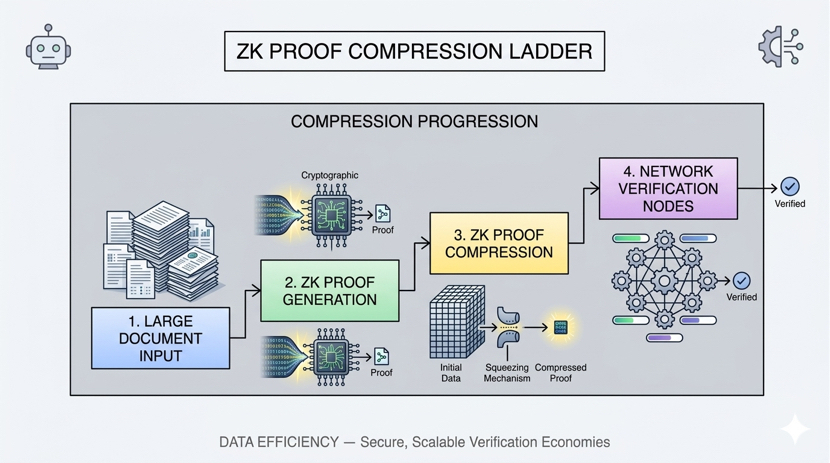
Under the hood this model relies on compact cryptographic verification systems such as
zk-SNARKs, which allow complex computations to be represented as small proofs that validators can check quickly.
The size difference between the original information and the proof can be dramatic.
A multi-megabyte document might produce a proof only a few kilobytes in size. The network verifies the smaller artifact while the full dataset remains outside the ledger.
What moves through the chain is not the record.
It is the mathematical guarantee derived from the record.
For developers, Midnight provides a programming environment designed to make this privacy model practical rather than theoretical. Contracts are structured to define both public and confidential components explicitly. Tooling built around TypeScript and Midnight’s Compact contract language allows applications to specify which data must remain private and which elements can interact directly with the chain.
The goal is not to hide transactions.
It is to hide the information transactions depend on.
That distinction becomes important as decentralized infrastructure begins moving beyond token transfers and into applications that deal with real economic and institutional activity.
Financial compliance systems, insurance verification, medical eligibility checks, supply chain certification. All of these processes require verification, but none of them can function if the underlying data becomes public infrastructure.
Midnight’s architecture suggests a different path.
The network verifies outcomes.
The participants keep their data.
If the experiment succeeds, blockchain systems may no longer need to choose between transparency and confidentiality.
Verification can still exist.
Consensus can still happen.
But the ledger no longer becomes a permanent archive of sensitive information.
Instead it becomes something closer to a referee.
It checks the proof.
It confirms the rules were followed.
And the records that produced those proofs remain where they always should have been.
With the people who own them.