I’ve been thinking a lot about machine identity lately. As robotics systems spread across industries, every autonomous machine effectively becomes a digital participant in a larger network. Robots inspect infrastructure, drones monitor environmental conditions, and automated systems manage logistics operations.
Each of these machines generates data and performs actions that other systems must trust. The more I observe this trend, the more I realize that identity for machines may become just as important as identity for people online. That is partly what led me to examine the cryptographic ideas emerging around the Fabric Protocol.
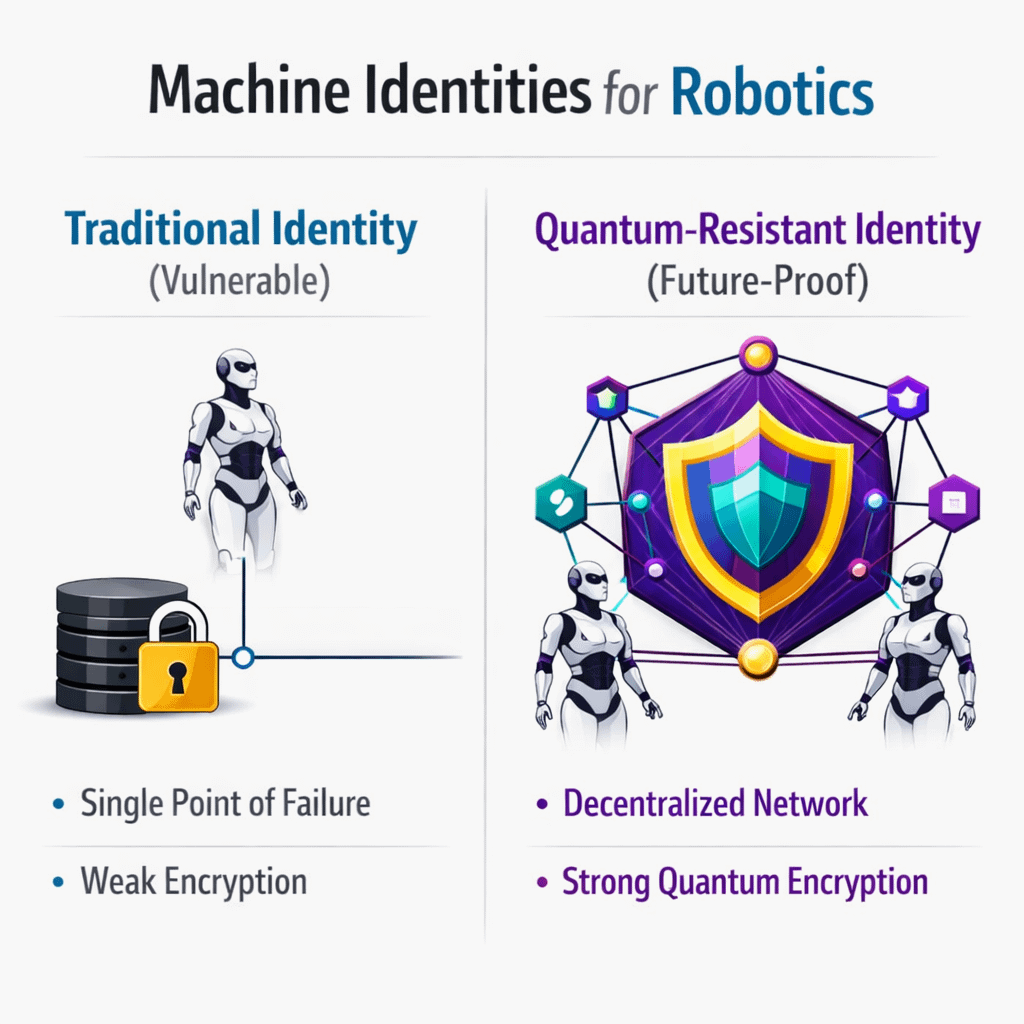
In traditional robotics environments, machine identity is usually managed through centralized systems. Devices are registered within a company’s internal infrastructure, and authentication happens through controlled access points.
For many industrial settings, this approach works perfectly well. But once machines begin operating across organizations or interacting with decentralized networks, identity becomes harder to manage.
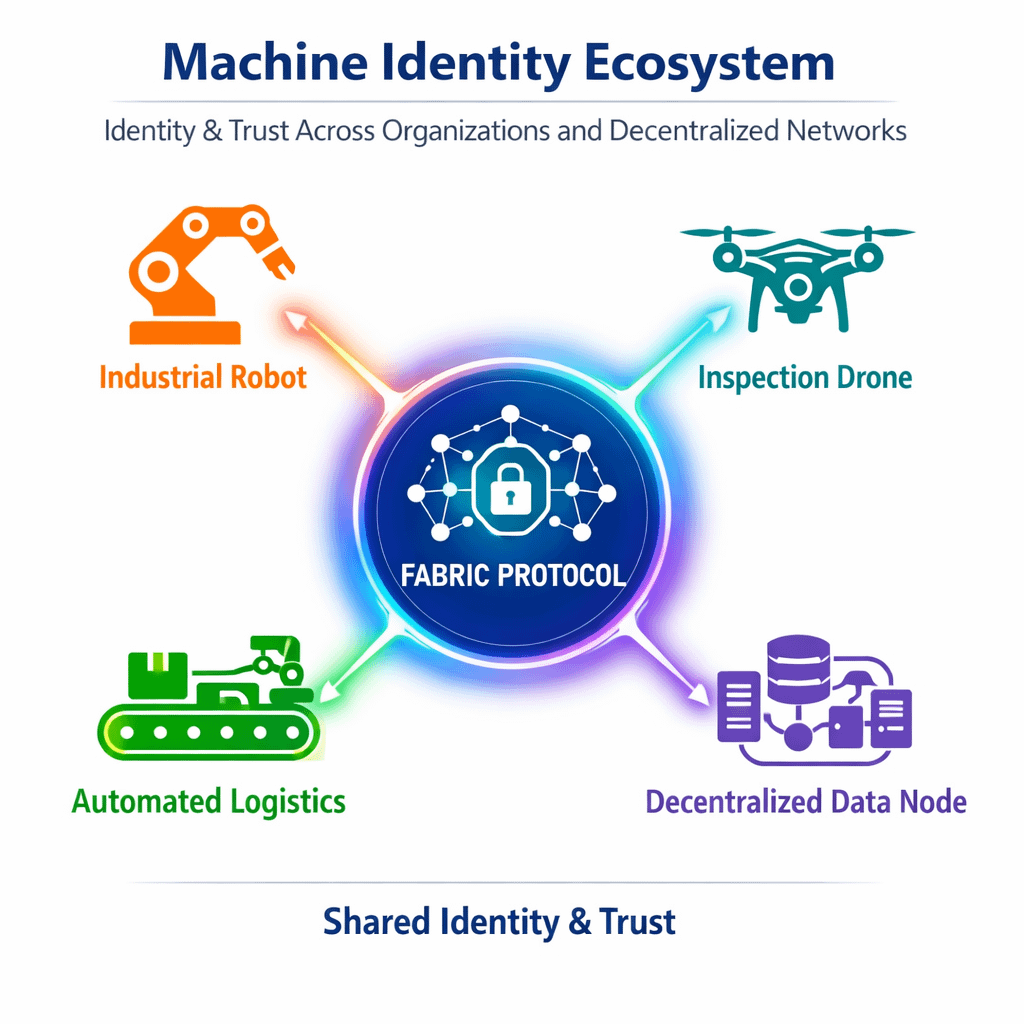
A robot inspecting infrastructure for one company might share data with another organization responsible for maintenance. A fleet of autonomous machines might operate across multiple logistics providers. In these environments, the system receiving information from a robot needs some way to confirm that the machine is exactly what it claims to be.
That sounds simple, but it raises a deeper issue.
Digital identity systems are built on cryptographic assumptions. Most of the internet relies on encryption methods that have proven reliable for decades. But the conversation around quantum computing has introduced a new layer of uncertainty. If quantum systems eventually become powerful enough to break certain cryptographic schemes, identity systems across many industries may need to evolve.
This is where the idea of quantum-resistant cryptography begins to appear.
From what I can see, the Fabric Protocol explores machine identity through cryptographic methods designed to remain secure even if computing power increases dramatically. The goal is not only to verify that a robot is authentic today but also to maintain that trust as the technological landscape changes.
I find that approach interesting because robotics infrastructure tends to last a long time.
Industrial robots, inspection drones, and automated systems often operate for years or even decades. The identity mechanisms protecting those systems cannot rely solely on cryptographic standards that may become outdated in the future.
If machines are expected to participate in decentralized networks for long periods, their identity frameworks must be designed with long-term resilience in mind.
Still, I try to approach these ideas carefully.
Quantum-resistant cryptography is still evolving, and the practical timeline for large-scale quantum computing remains uncertain. Some experts believe the threat is decades away, while others argue that preparation should begin now.
Designing infrastructure for robotics networks around quantum-resistant principles could be forward-thinking, but it also introduces complexity.
Another factor I keep considering is integration.
Robotics systems already operate within complicated technical stacks. Sensors, control systems, AI models, and communication protocols must work together reliably. Introducing new cryptographic layers into that environment requires careful engineering to avoid slowing down machine operations.
Machines working in real-time environments cannot afford significant delays in authentication or verification processes. Any identity system supporting robotics must remain lightweight enough to function within those operational constraints.
Despite these challenges, the concept of secure machine identity continues to feel increasingly important.
As robotics networks expand, machines are no longer isolated devices operating within a single company’s infrastructure. They are becoming participants in larger ecosystems where data and actions influence multiple stakeholders. In those environments, verifying the authenticity of a machine becomes essential.
The Fabric Protocol’s exploration of cryptographic identity for machines suggests an attempt to build infrastructure that anticipates these future conditions. Rather than treating robotics as isolated systems, the protocol appears to approach machines as actors within decentralized networks where identity, verification, and security all play critical roles.
Whether quantum-resistant cryptography ultimately becomes necessary for robotics networks remains uncertain. Technological forecasts often change as new discoveries appear. But what feels increasingly clear to me is that machine identity will play a central role in the next generation of automated systems.
If robots continue expanding across industries and begin interacting more directly with decentralized infrastructure, the mechanisms that verify who those machines are may quietly become some of the most important components of the systems supporting them.