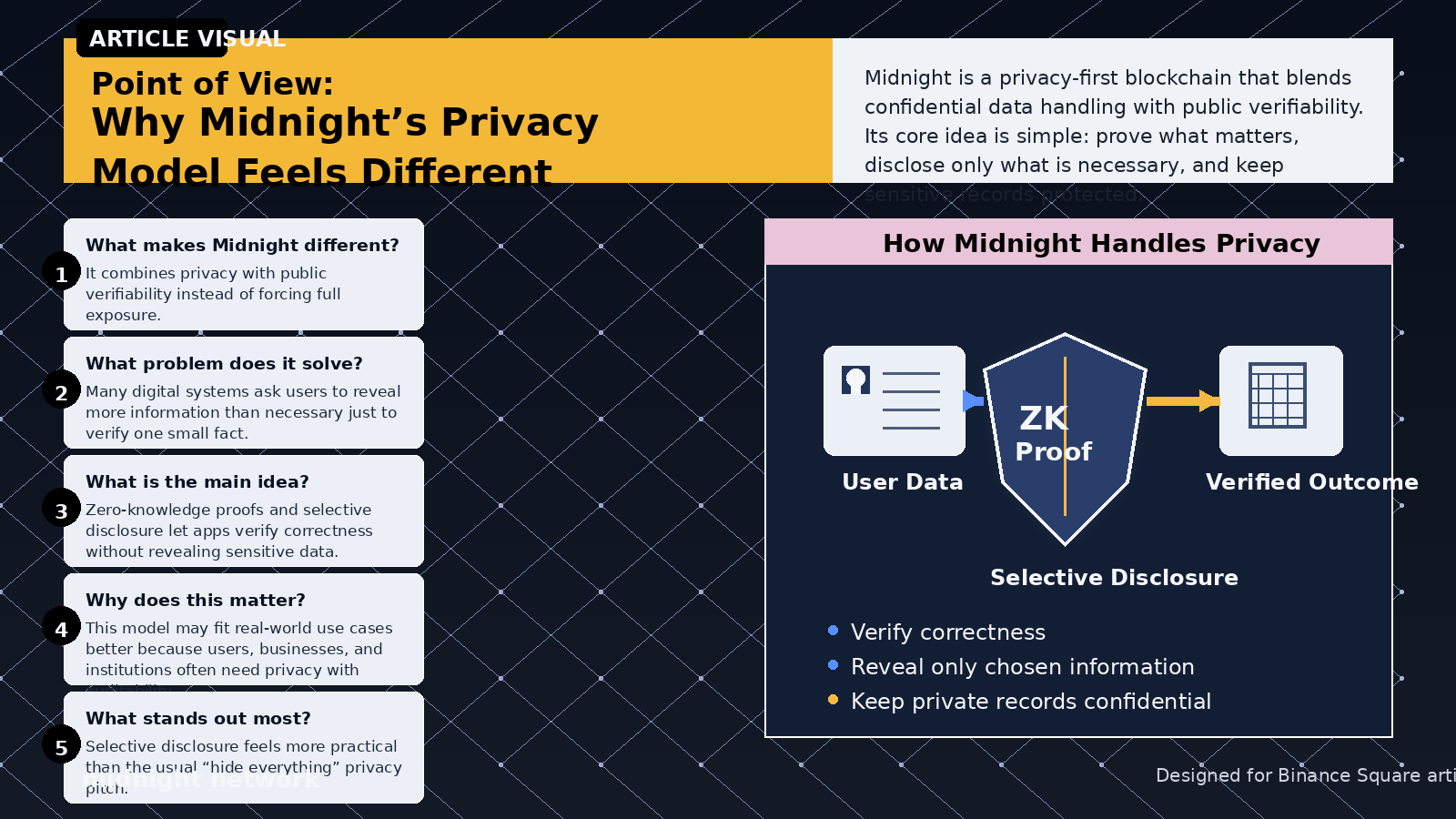
I can see why Midnight is getting attention right now. On paper, the case is strong. Midnight describes itself as a privacy-first blockchain that combines confidential data handling with public verifiability, and its docs repeatedly frame the network around selective disclosure rather than blanket secrecy. The pitch is easy to understand: let users and applications prove what matters without exposing everything underneath. In a market where most chains still default to radical transparency, that is a real and serious proposition.
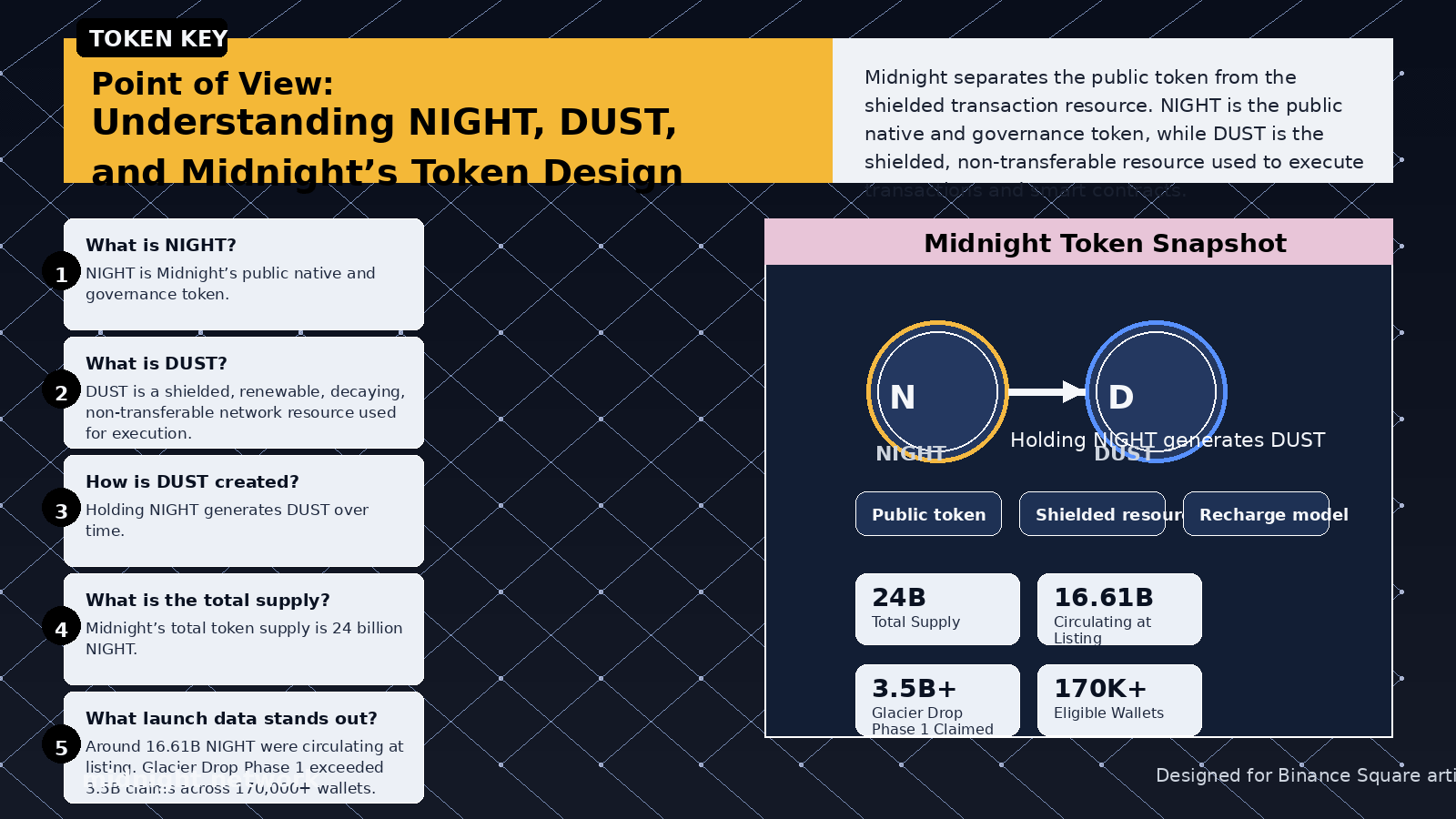
What makes the design more interesting is that Midnight is not just selling privacy as philosophy. Its token model is unusually concrete. NIGHT is the public native and governance token, while DUST is a shielded, non-transferable resource used to execute transactions and smart contracts. Holding NIGHT generates DUST over time, and Midnight explicitly presents that as a battery-style model that can make operational costs more predictable and even let developers subsidize usage for end users. That is not just tokenomics theater. It is a specific attempt to make privacy-preserving infrastructure usable at application level.
But the more coherent the architecture looks, the more one question keeps bothering me: what exactly does accountability look like when something goes wrong inside a system built to hide sensitive state and metadata?
That is where I think the real tension begins. Midnight argues that its structure is both confidential and auditable: data, proofs, shielded transaction data, and DUST usage remain private, while settlement and consensus remain public through the NIGHT ledger. That distinction is meaningful. But it also has limits. Auditability of settlement is not the same thing as auditability of application behavior. If a privacy-preserving lending app, payroll system, or identity workflow fails in production, the public may be able to see that something happened without being able to reconstruct why it happened. Midnight can say the proof verified correctly. The harder question is whether the contract logic deserved to be trusted in the first place.
That difference matters more than people admit. Proof systems verify what they are designed to verify. They do not automatically catch flawed assumptions, incomplete edge-case modeling, or bad contract architecture. In transparent environments, exploits are ugly but legible. Analysts can trace state changes, inspect transactions, and reconstruct failure in public. In a privacy-preserving environment, failure can become harder to interpret precisely because the system is doing what it was built to do: hiding details. That does not make Midnight broken. It means Midnight may eventually face a deeper burden than ordinary infrastructure projects. It has to prove not only that privacy works, but that post-failure trust can survive when visibility is intentionally reduced.
I think this gets even more important when you look at developer accessibility. Midnight’s site says it is optimized for rapid integration and built around Compact, a smart contract language based on TypeScript that is meant to reduce the steep cryptographic learning curve for developers. That is clearly a strength. Better tools are how ecosystems grow. But easier tooling also means more teams, with uneven security discipline, building privacy-sensitive applications that users may not fully understand. When the builder base expands, the quality distribution expands too. And opaque execution plus wider developer access is not automatically a safe combination.
That is why I do not think Midnight’s biggest challenge is explaining privacy. Its biggest challenge may be explaining failure. The network already has a coherent story for why selective disclosure matters, why NIGHT and DUST are separated, and why privacy should not mean anonymous value transfer. What I still want to see more clearly is the public-accountability model for the day a major Midnight application breaks under real economic pressure. Because that is when architecture stops being theory and starts becoming social reality. And if that answer depends too heavily on developer cooperation rather than independent public reconstruction, then the trust assumptions may not have disappeared at all. They may have just moved.