@MidnightNetwork One evening I found myself scrolling through a block explorer again, watching transactions settle across several networks. Wallet addresses moved value back and forth while the underlying logic stayed perfectly transparent. Every timestamp. Every transfer amount. Every interaction visible to anyone patient enough to read it.
For years the industry treated that visibility almost like a philosophical principle. Radical transparency was supposed to be the solution to trust. If everyone could see the ledger, nobody needed to rely on institutions.
But lately that assumption feels less stable.
The deeper blockchain systems move into real economic activity, the more unusual that level of exposure starts to look. In traditional financial systems, the settlement layer is visible to regulators and institutions, but the operational details inside agreements remain mostly private. Corporate treasury flows, derivatives positions, internal liquidity transfers — these activities rarely sit on fully public infrastructure.
Crypto reversed that structure. And it worked for a while.
Yet the question now surfacing around systems like Midnight Network is whether the next phase of blockchain infrastructure requires a different balance. Instead of abandoning transparency entirely, the idea is to separate verification from disclosure.
At first glance, Midnight appears to explore that separation.
Observers often describe the network simply as a privacy chain. But that description misses something important. Midnight does not attempt to hide the entire system. Instead, it introduces a dual structure where sensitive logic can operate privately while settlement signals still reach a public layer.
That architectural shift changes how one interprets the role of the $NIGHT token.
Many privacy-oriented systems historically built their tokens around shielding transactions themselves. Midnight approaches the problem differently. NIGHT remains an unshielded token, visible on the ledger, used for governance and network security. What it generates, however, is a secondary computational resource called DUST, which powers the confidential execution of smart contracts.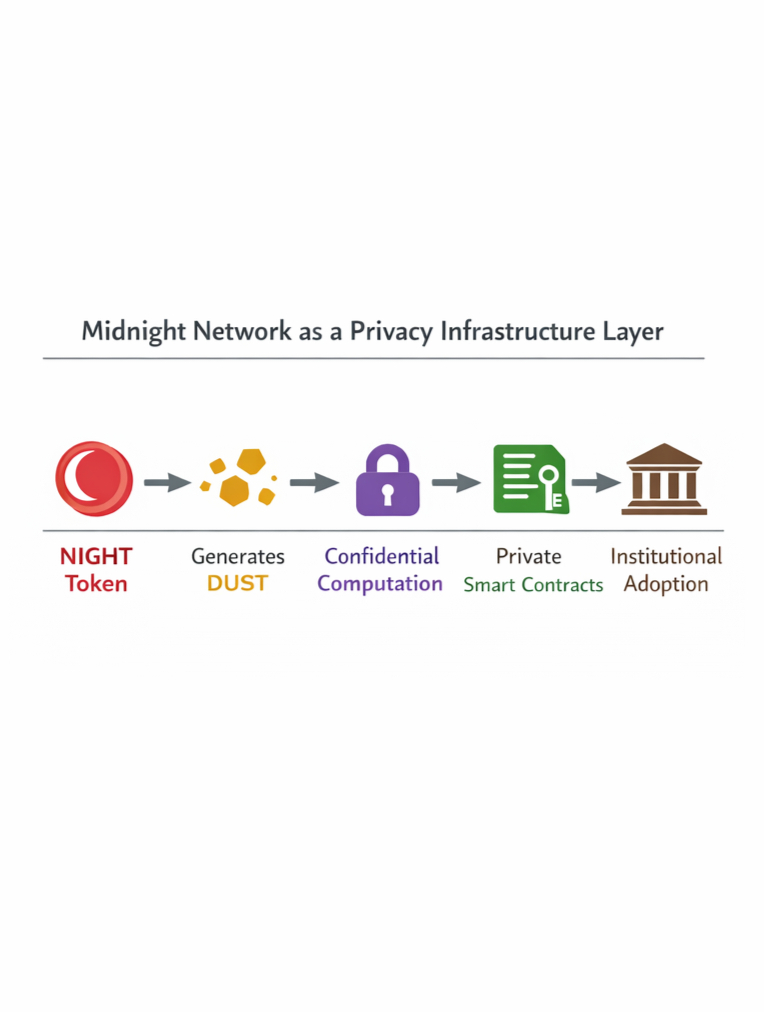
The distinction is subtle but meaningful.
From the outside, observers see normal token activity moving through the system. Underneath that surface layer, the computational work required for private execution happens through a different mechanism. Zero-knowledge circuits validate contract logic without revealing the data those contracts process.
In practice, this means the network does not attempt to obscure settlement entirely. Instead it allows agreements to run quietly while still producing verifiable outcomes.
That structure begins to make more sense when viewed against the scale modern crypto markets have reached. Global digital asset trading frequently moves $60–80 billion in daily exchange volume, depending on market cycles. Liquidity now circulates through centralized exchanges, decentralized protocols, and derivatives venues simultaneously.
Every one of those flows produces data.
When institutional capital enters that environment, transparency stops looking purely beneficial. Large funds rarely want their trading strategies visible to competitors in real time. Corporate treasury operations do not typically broadcast internal transfers to the public internet.
In traditional markets, privacy functions as a form of coordination stability.
Midnight seems to be experimenting with how similar coordination might work in decentralized infrastructure. Instead of forcing all contract logic into public visibility, the network allows information to remain local while still proving that the computation occurred correctly.
The cryptographic backbone enabling this approach is zero-knowledge proof technology.
At the surface level, zero-knowledge systems allow one party to prove a statement is true without revealing the underlying data. Observers often frame this as a privacy trick. But beneath that explanation sits something more structural.
The proofs allow computation to separate from verification.
A contract can process inputs privately. Then it produces a proof confirming that the logic followed predefined rules. Validators check the proof rather than the data itself. The system maintains integrity without exposing sensitive information.
For coordination between institutions, that distinction matters.
Imagine two firms negotiating a derivatives position on-chain. The settlement outcome needs to be verifiable. The internal pricing model, risk thresholds, or hedging logic likely does not.
If Midnight’s architecture works as intended, those layers could coexist.
The public ledger records the settlement signal. The contract’s internal mechanics remain shielded inside the zero-knowledge execution environment.
Still, technical elegance does not automatically translate into network adoption.
One structural tension sits in the economics of privacy infrastructure itself. Confidential execution typically requires heavier computation than simple public transactions. Generating proofs consumes processing resources and time.
That is where Midnight’s DUST resource model becomes interesting.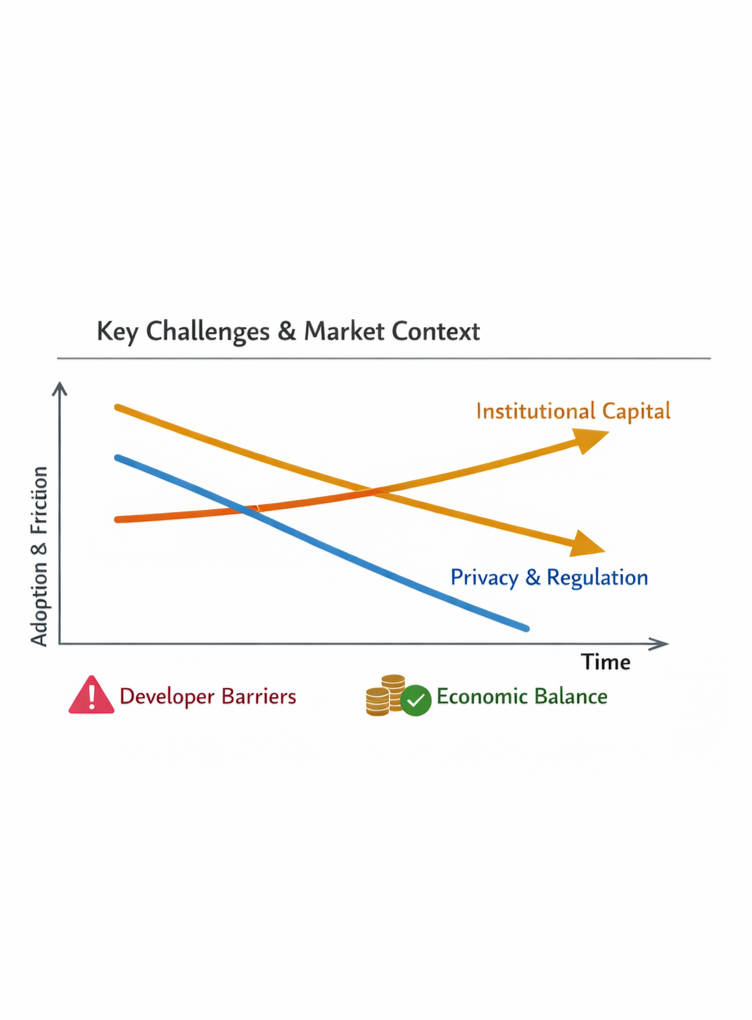
Rather than pricing computation directly through token fees alone, the network introduces DUST as a derived resource tied to NIGHT holdings. In theory this mechanism attempts to balance demand for private execution with network capacity.
The design resembles energy budgeting more than simple transaction fees. Users consume computational allowance when running confidential contracts, which may help prevent abuse of the system.
But it also raises questions.
If privacy infrastructure becomes widely used, computational demand could rise sharply. Networks must ensure proof generation remains efficient enough to support large transaction flows without creating bottlenecks.
Recent zero-knowledge ecosystems show both progress and challenges here. Some modern ZK rollups now process thousands of transactions per batch, compressing large volumes of activity into a single verification proof. Yet proof generation still requires significant hardware resources.
Scaling confidential computation remains a moving target.
Regulation introduces another layer of uncertainty.
Privacy technologies often attract scrutiny because regulators worry about illicit financial activity. Yet the design choices behind Midnight suggest an attempt to avoid complete opacity. The settlement layer remains visible, and governance occurs through the transparent NIGHT token.
This hybrid structure could potentially align better with regulatory expectations than fully shielded financial systems.
But policy responses to privacy infrastructure remain unpredictable. Governments across several jurisdictions continue exploring frameworks around digital asset transparency and anti-money-laundering compliance.
The network’s long-term trajectory may depend partly on how those rules evolve.
Beyond regulation, developer adoption will likely determine whether Midnight evolves into genuine infrastructure or remains a niche experiment. Blockchains become meaningful when other systems start building on top of them.
Developers generally look for predictable environments: stable execution, accessible tooling, and clear economic incentives.
If Midnight successfully abstracts complex zero-knowledge logic behind developer-friendly frameworks, its privacy capabilities could become more widely usable. If the system remains technically demanding, adoption may move slowly.
Interestingly, broader industry signals hint that demand for privacy-preserving infrastructure is increasing. Institutional crypto ETFs now hold tens of billions of dollars in digital assets, while traditional financial firms experiment with tokenized securities and on-chain settlement systems.
These institutions often expect a level of operational discretion that public blockchains struggle to provide.
In that context, privacy layers begin to look less like optional features and more like missing infrastructure components.
Midnight appears to position itself inside that gap.
Whether it succeeds will depend less on philosophical debates about privacy and more on practical coordination dynamics. Systems gain traction when they quietly reduce friction for participants moving real value.
If confidential execution allows institutions, developers, and decentralized applications to operate without exposing sensitive logic while still settling on open networks, the architecture could become increasingly relevant.
Seen from that perspective, the NIGHT token is not simply a governance asset.
It functions more like an anchor for a computational environment designed to balance transparency with discretion.
And if that balance proves workable under real economic pressure, Midnight may end up representing something larger than a privacy chain — it could become one of the early attempts to design a confidential infrastructure layer for open financial systems.#night