Spending enough time in cryptocurrency markets teaches you to recognize a familiar pattern: sometimes the narrative surrounding an idea begins accelerating faster than the infrastructure meant to support it. Privacy has consistently been one of those narratives. Every few market cycles, the industry revisits the same compelling promise—confidential transactions, private smart contracts, and encrypted computation operating within decentralized networks.
When this conversation returns, traders usually respond quickly. Market attention rotates toward privacy-focused technologies, and speculation begins about whether confidential computation could eventually become a foundational layer of blockchain systems. Yet the same question always emerges beneath the excitement: is it possible to safeguard sensitive data without undermining the transparency that public blockchains rely on? That tension provides an interesting lens through which to observe the growing attention surrounding @MidnightNetwork and the broader discussion forming around the NIGHT ecosystem.
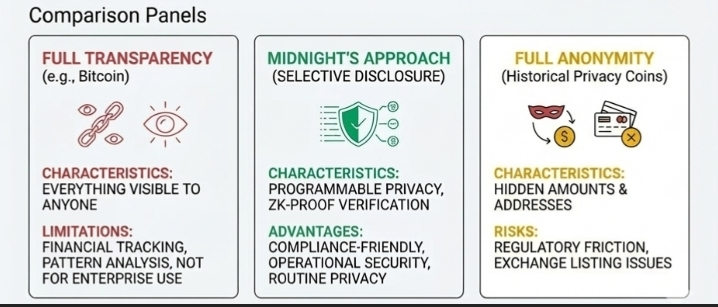
The challenges facing privacy-oriented blockchain projects are far from theoretical. Public blockchains were originally designed around radical openness. Every transaction, wallet balance, and contract interaction is visible to anyone running a node or browsing a block explorer. This transparency is what allows decentralized networks to verify activity without relying on a central authority.
However, the same openness becomes more complicated as blockchain technology begins interacting with broader economic systems. Businesses rarely want competitors analyzing their operational transactions in real time. Developers building enterprise-grade applications cannot always publish internal data permanently on a public ledger. Even individual users may feel uneasy knowing that every payment they make could reveal long-term patterns about their financial behavior. Anyone who has followed wallet activity through a blockchain explorer understands how quickly transaction histories can be mapped, analyzed, and connected.
This is where Midnight’s broader vision begins to stand out. The project is exploring a concept increasingly referred to by developers as programmable privacy. Rather than hiding all information completely, the goal is to create systems where users and applications can selectively determine which information remains confidential and which elements become publicly verifiable.
In practice, this means a transaction or smart contract interaction could prove that certain conditions were satisfied without revealing the underlying data itself. These systems often rely on sophisticated cryptographic techniques such as zero-knowledge proofs, allowing one party to verify the truth of a statement without exposing the information that produced it. If implemented effectively at scale, such an approach could create a meaningful balance—preserving confidentiality while maintaining the verifiability that decentralized systems require.
For market participants, the recurring interest in this concept is not surprising. Blockchain networks are evolving beyond simple token transfers into far more complex environments that include decentralized finance, application ecosystems, and data coordination layers. As these systems expand, the demand for selective confidentiality grows alongside them.
Organizations experimenting with decentralized infrastructure often need to protect internal financial operations. Developers designing financial applications may require privacy-preserving tools that remain compatible with regulatory frameworks. Even everyday users are beginning to recognize that complete, permanent transparency may not always be ideal for ordinary economic activity. Midnight’s broader ambition appears to revolve around building infrastructure where confidential information can interact seamlessly with verifiable blockchain systems—without compromising either side of the equation.
Historically, however, privacy-focused networks have faced unique pressures. Governments and regulatory bodies often approach strong encryption and anonymous financial tools with caution, particularly when issues such as financial oversight and anti-money-laundering regulations are involved. This tension has influenced the development of numerous privacy projects over the past decade.
Some networks struggled to maintain exchange listings, while others redesigned their architectures to allow varying degrees of transparency when necessary. Midnight appears to be exploring a more balanced approach by emphasizing selective disclosure rather than total anonymity. If executed carefully, such a framework could allow privacy infrastructure to coexist with compliance expectations without abandoning the transparency principles that define blockchain systems.
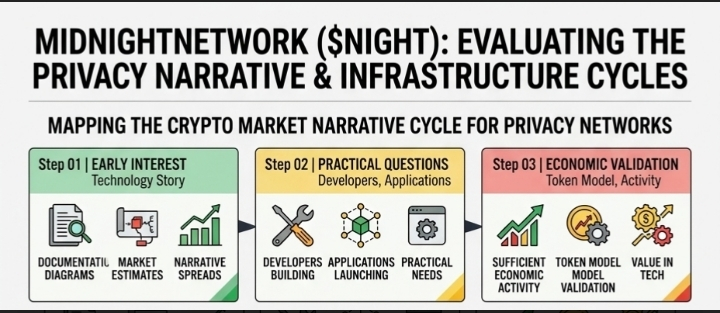
From a market perspective, narratives like this typically follow a familiar trajectory. Early enthusiasm often centers on the technology story itself. Traders examine documentation, analyze architectural diagrams, and attempt to estimate the potential size of the market opportunity. When the narrative intersects with broader themes—such as data security, privacy rights, or modular blockchain architecture—it can spread rapidly throughout the ecosystem.
Yet narratives rarely sustain momentum indefinitely. Eventually, the discussion shifts toward more practical questions. Are developers actively building on the network? Are real applications launching that rely on these privacy capabilities? And perhaps most importantly, does the ecosystem generate enough genuine economic activity to sustain the token model behind it?
Evaluating privacy infrastructure can be particularly difficult because much of its value lies in areas that are not immediately visible. The real breakthroughs often occur in cryptographic design, developer tooling, and network performance—areas that traders observing from the outside rarely experience directly. Instead, they rely on indirect indicators: developer engagement, ecosystem partnerships, integrations with other protocols, and the gradual emergence of applications built specifically around the technology.
Another challenge involves balancing technical sophistication with accessibility. Advanced cryptographic systems unlock powerful capabilities, but they also introduce complexity. If those systems become too difficult for developers to implement—or too resource-intensive for practical use—adoption tends to slow. The infrastructure projects that succeed over the long term usually reach a stage where developers can build applications without needing to fully understand the cryptographic machinery operating beneath the surface.
Whether Midnight can achieve that level of usability is something the broader market will likely observe closely as the ecosystem develops.
For traders and observers, a practical mindset often involves separating narrative momentum from infrastructure timelines. Privacy will almost certainly remain a central topic as decentralized technology evolves. But transforming that idea into reliable developer platforms, real-world applications, and sustainable economic ecosystems requires patience. The gap between those stages is where much of the uncertainty—and opportunity—tends to exist.
This is precisely why Midnight deserves attention right now. Not because privacy itself is a new concept, but because the industry is gradually moving toward systems where confidentiality and transparency must coexist. If @MidnightNetwork succeeds in delivering tools that developers consistently adopt, it could become part of a larger shift toward programmable privacy within decentralized infrastructure.
If adoption remains limited, however, the narrative may remain more conceptual than operational.
For now, patience remains the most valuable perspective. Narratives move quickly in crypto markets, but infrastructure reveals its real value slowly. Traders watching NIGHT and the broader privacy discussion will likely learn more from long-term developer activity and ecosystem growth than from short-term waves of market enthusiasm.
In the end, the distinction between a compelling idea and a durable network usually becomes clear only after the narrative quiets—and the builders continue working regardless.
@MidnightNetwork
#night
$NIGHT