While exploring the ecosystem around $NIGHT, I realized something important about @MidnightNetwork: it is not just another privacy narrative in crypto. It is an attempt to redesign how information flows on a blockchain.
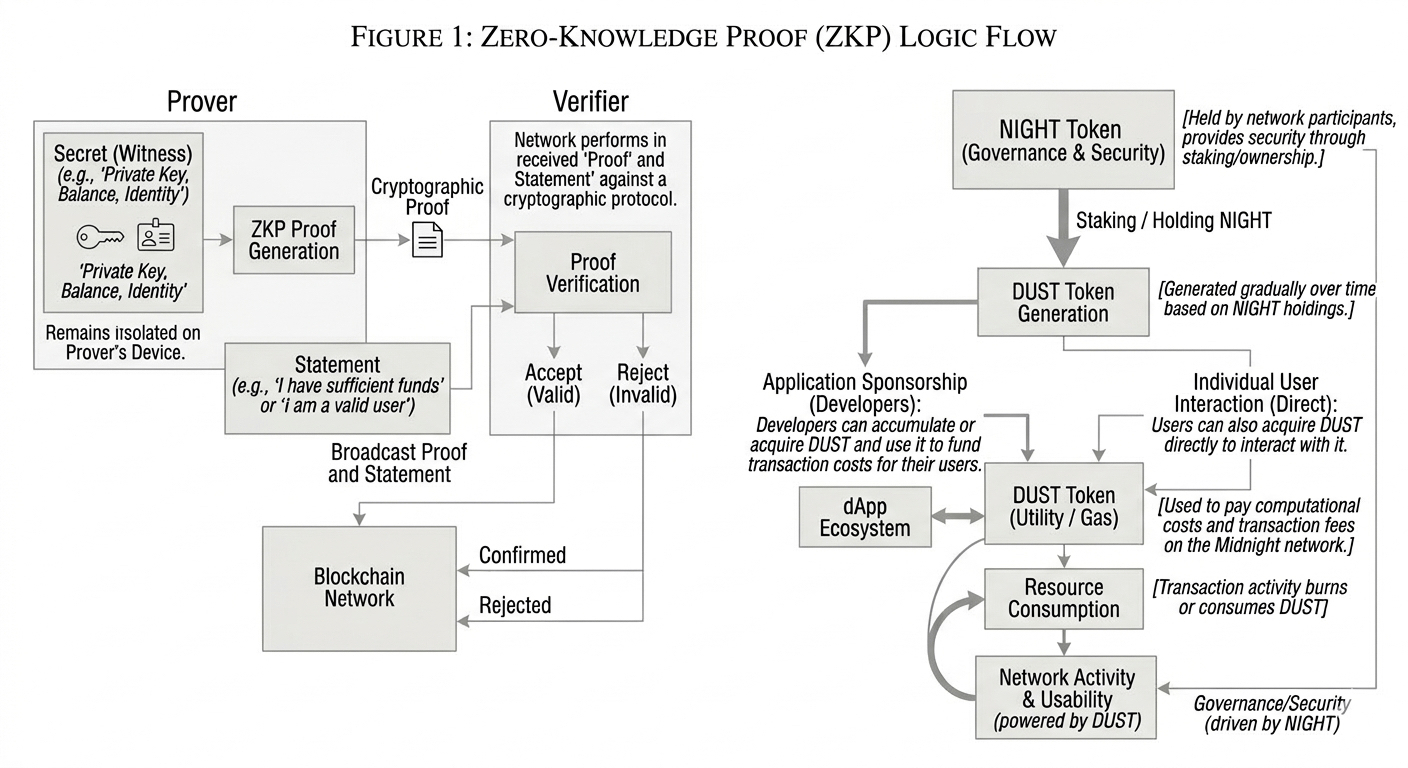
Most people assume privacy projects are about hiding everything. Midnight approaches the problem differently. Instead of asking how data can disappear from view, the project asks a more difficult question: can truth be verified without exposing the underlying information?

That difference may sound subtle, but it changes the entire philosophy of blockchain design.

A Devnet Built for Real Experimentation
The Midnight devnet, launched in 2023, is more than a testing environment. It feels like a playground for privacy development. Developers can experiment with privacy-protecting smart contracts and test business logic locally before deploying it to a public chain.

What stood out to me is how accessible the tools are.
Midnight created a smart-contract language called Compact, which resembles TypeScript. Since many developers already know TypeScript, this lowers the barrier to entry significantly. Compact allows developers to clearly define which parts of a contract are private and which parts are public, while removing complex features that would make verification difficult.
Developers can compile contracts, deploy them directly to the devnet, and interact with them using a browser wallet. Applications can then be shared with other testers for experimentation.
The devnet even uses a special testing token called tDUST. Testers obtain it through a faucet and use it to pay fees or transfer shielded assets while experimenting with privacy applications.
This environment encourages exploration. Developers can:
generate zero-knowledge proofs locally
interact with Midnight assets through a browser extension
read blockchain data using pub-sub services
build applications with a dedicated VS Code extension
One detail I find particularly important is that most of these tools run directly on the developer’s machine. Sensitive information never needs to be sent to remote servers.
The proof server typically runs locally as a Docker container, while wallets communicate directly with it. This architecture allows developers to build applications that meet strict data-protection requirements. Personal or financial data can remain off-chain while still proving that rules or compliance conditions were satisfied.
In practice, this turns the idea of programmable privacy into something tangible.
Privacy Doesn’t Mean Disappearing
Another reason Midnight caught my attention is how it reframes the concept of privacy.
Older privacy projects often pushed toward complete concealment. Everything hidden, everything opaque. But that approach rarely fits how real systems operate.
Companies, institutions, and even individuals usually do not want to vanish from view. They simply want to avoid exposing ten layers of sensitive information just to prove one small thing.
Midnight’s concept of selective disclosure tries to solve exactly that problem.
A person should be able to prove eligibility without revealing their entire identity history.
A business should execute logic without exposing internal operational details.
A network should verify that something is valid without turning every interaction into a permanent public archive.
Instead of radical transparency or total secrecy, Midnight aims for controlled information flow.
And honestly, that feels overdue.
For years, crypto treated full transparency as a virtue. But in practice, constant exposure often leads to surveillance, data leakage, and systems that technically work yet feel hostile to their users.
Midnight appears to challenge that assumption without falling into the trap of making secrecy its entire identity.
The DUST Debate and Honest Design
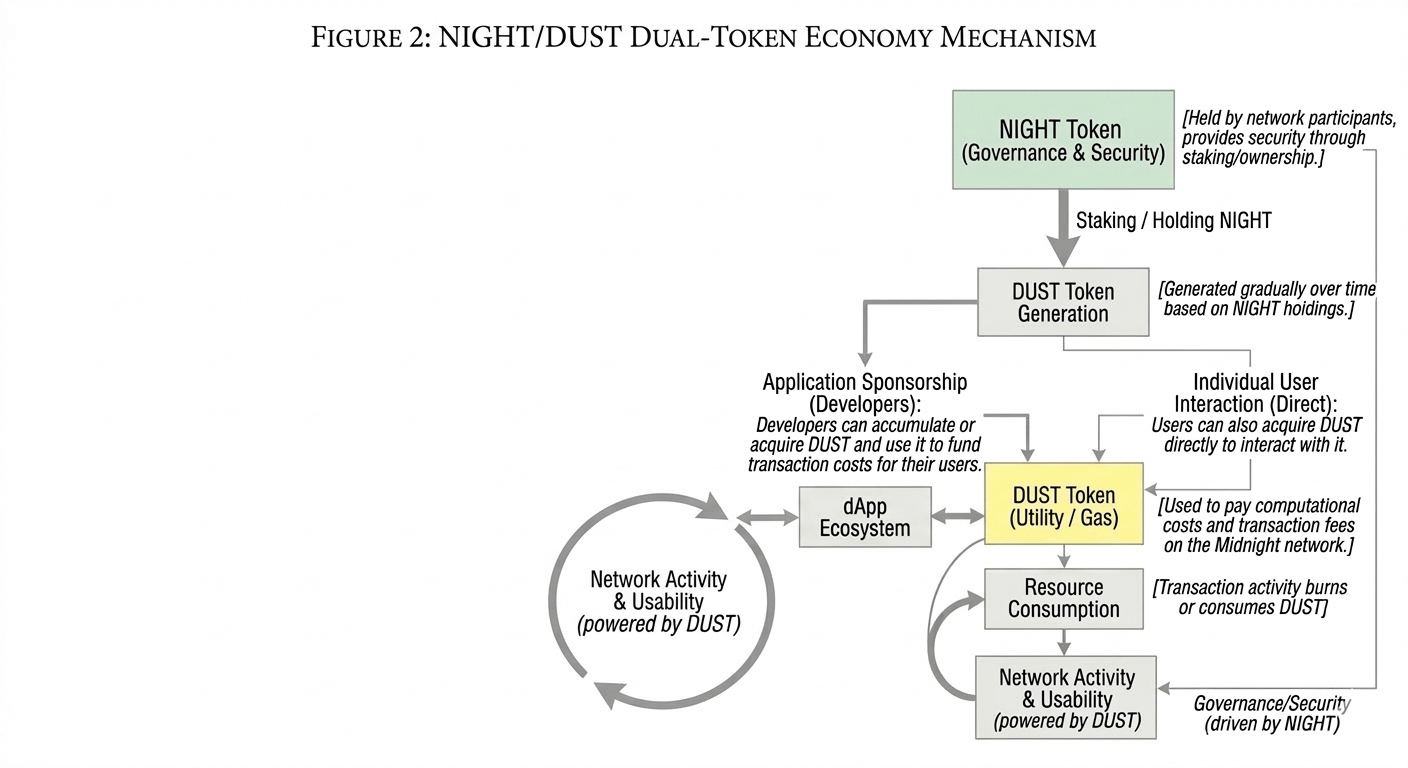
While researching Midnight, I also came across discussions around the project’s DUST mechanism.
An experienced developer from the Cardano ecosystem raised a criticism: if holders generate DUST from $NIGHT, could attackers spam the network cheaply?
Interestingly, Midnight does not hide this concern. The official tokenomics documentation openly states that holding enough NIGHT could allow a user to generate DUST and attempt spam transactions.
That level of transparency is rare.
However, the system is designed so that spam is not actually free.
Each transaction requires generating a zero-knowledge proof, which is computationally expensive. If the network becomes congested, the dynamic pricing mechanism increases the required DUST cost. Transactions with insufficient DUST are rejected and must be resent with a new proof, increasing the attacker’s computational expense.
In addition, DUST generation is limited by the amount of NIGHT held and grows linearly per block. It cannot be accumulated indefinitely.
Still, the criticism is not entirely invalid. Large infrastructure actors might have enough resources to attempt coordinated spam attacks during the early stages of the network.
Midnight acknowledges this as well.
At launch, block producers receive around 95% of rewards regardless of block usage, which could reduce incentives to reject spam transactions. The plan is to reduce this subsidy to around 50% as the network matures.
This does not prove the design is perfect. But it does suggest the team is willing to confront weaknesses before the system goes live rather than pretending they do not exist.
In an industry filled with marketing optimism, that honesty is refreshing.
Federated Mainnet and the Road Ahead
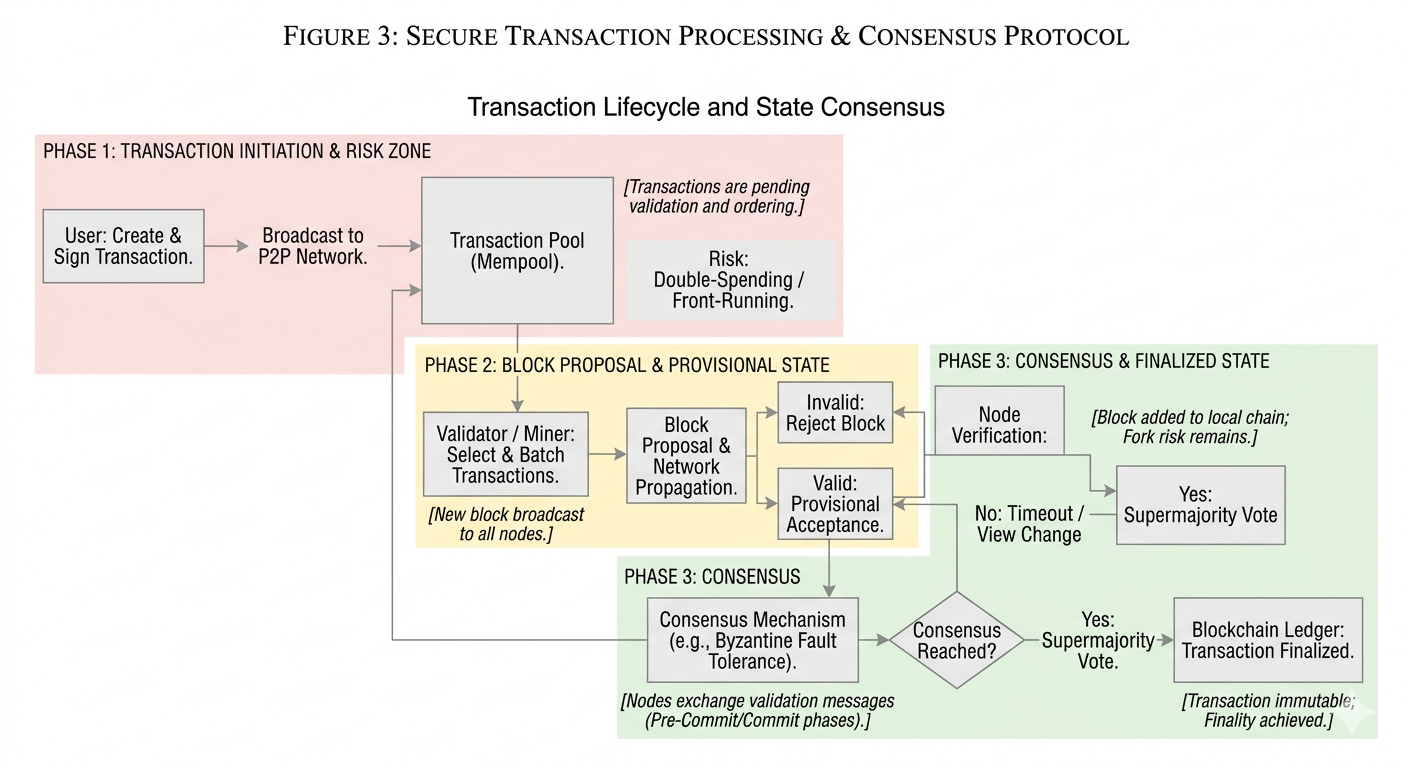
The early Midnight mainnet will begin as a federated network, with node operators including major infrastructure providers such as cloud services and blockchain infrastructure companies.
Yes, this introduces temporary centralization. But it also allows the network to stabilize before transitioning to broader decentralization.
History shows that most blockchains learn about spam and congestion after launch, not before. Ethereum needed multiple upgrades and fee redesigns to handle network congestion. Solana experienced several spam-induced outages before implementing priority fees.
There is rarely a perfect design from day one.
What matters is whether the system can adapt.
Why Midnight Feels Different
Many crypto projects chase attention first and purpose later.
Midnight feels built in the opposite order.
The project is not trying to make blockchain louder. It is trying to make it less careless with data.
That difference might not generate immediate hype. But it addresses a real structural problem in blockchain architecture: how to balance verification, privacy, and usability at the same time.
If selective disclosure becomes practical infrastructure rather than a niche feature, Midnight could play an important role in the next generation of blockchain applications.
If not, it may simply become another thoughtful project the industry admires and moves on from.
For now, the devnet experimentation, the programmable privacy model, and the honest design discussions suggest something interesting is taking shape.
The real test will begin when the network moves beyond theory and faces real usage, real developers, and real pressure.
Until then, Midnight remains one of the more intriguing attempts to make blockchain not just transparent, but intelligently private.
#night $NIGHT @MidnightNetwork