Mira taught me about Data Provenance on Thursday afternoon.
We've had a partner integration work seamlessly. Then a routine audit uncovered a misalignment. A receipt supposed to link to the corresponding source document linked to some other document. Not an incorrect answer, an incorrect origin.
The claim was okay, the decision was okay, but the receipt was an incorrect pointer. The structure eroding claim to evidence had drifted, and no one noticed it until a human auditor came and did the tedious work of tracing the pointer back.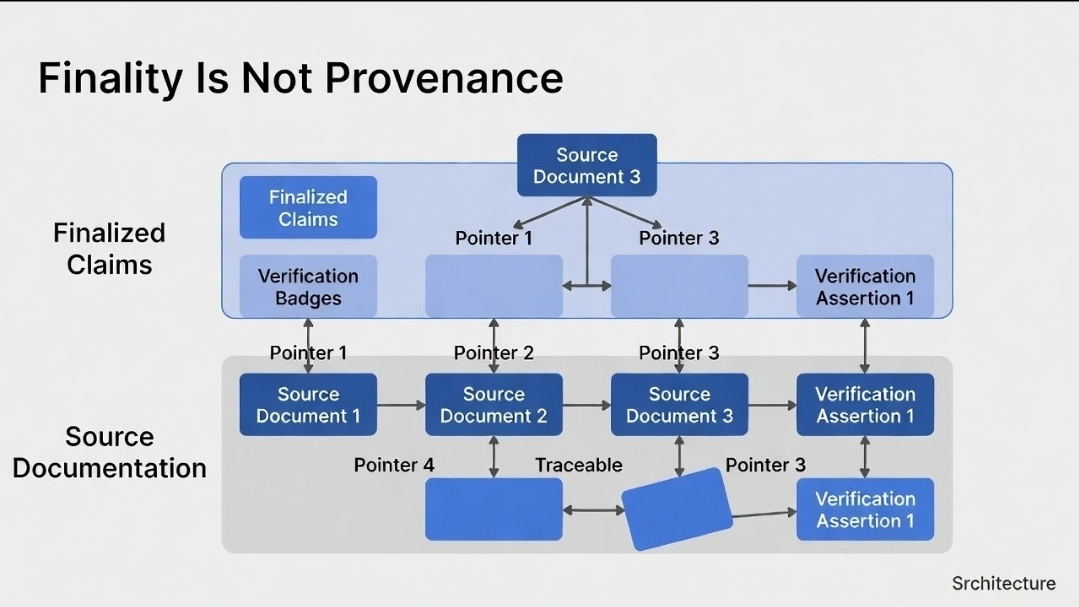
When provenance is ignored in a network, the network is productive.
Mira is designed to allow proof to speak. Decompose the output into claims, verify them across independent provers, and finalize them through proof and consensus. This process results in receipts that are proverbial and final. The surface, in a sense, is not finality. It is the pointer that connects a final claim to the primitive from which it was derived.
A verdict tells you what happened, but a receipt tells you where to look if you don't believe it.
Once the provenance gets out of hand, trust becomes a manual look up. These pointers allow an operator to walk a claim back to every verifier that touched it. If that thread breaks, the receipt is decorating. It certifies something that is not true.
The mechanism is quite clever. Output in Mira gets broken down into claims. Each different verifier is checking a different slice. Each one comes up with a signed assertion. These paired with the others make up a final receipt. If the assertion’s source is ambiguous, if a hash is pointing to something that doesn’t exist anymore, the receipt is a conclusion without a chain.
That ambiguity does not need malice. Ordinary scaling is enough. A retention policy that prunes old inputs. A migration that rewrites identifiers. A verifier saving context. Each one is rational, but in combination they result in receipts that are theoretically valid but practically invalid.
Auditing becomes guesswork once the receipts become opaque. That’s when teams often construct a second system. A reviewer starts retrieving raw logs in parallel to the receipts. Belt-and-suspenders, described as temporary. Then reconciliation begins to expand. Then the audit lane becomes permanent. Verification systems reintroduce manual review without a single line of code being altered. It’s not a failure to finalize. It’s finalizing objects that are defenseless.
Metric compliance teams keep track of, among other things, unreplayable receipts per 100 audits. With 12 such receipts, trust turns into investigations. Operators start demanding screenshots. No receipts, no autonomy.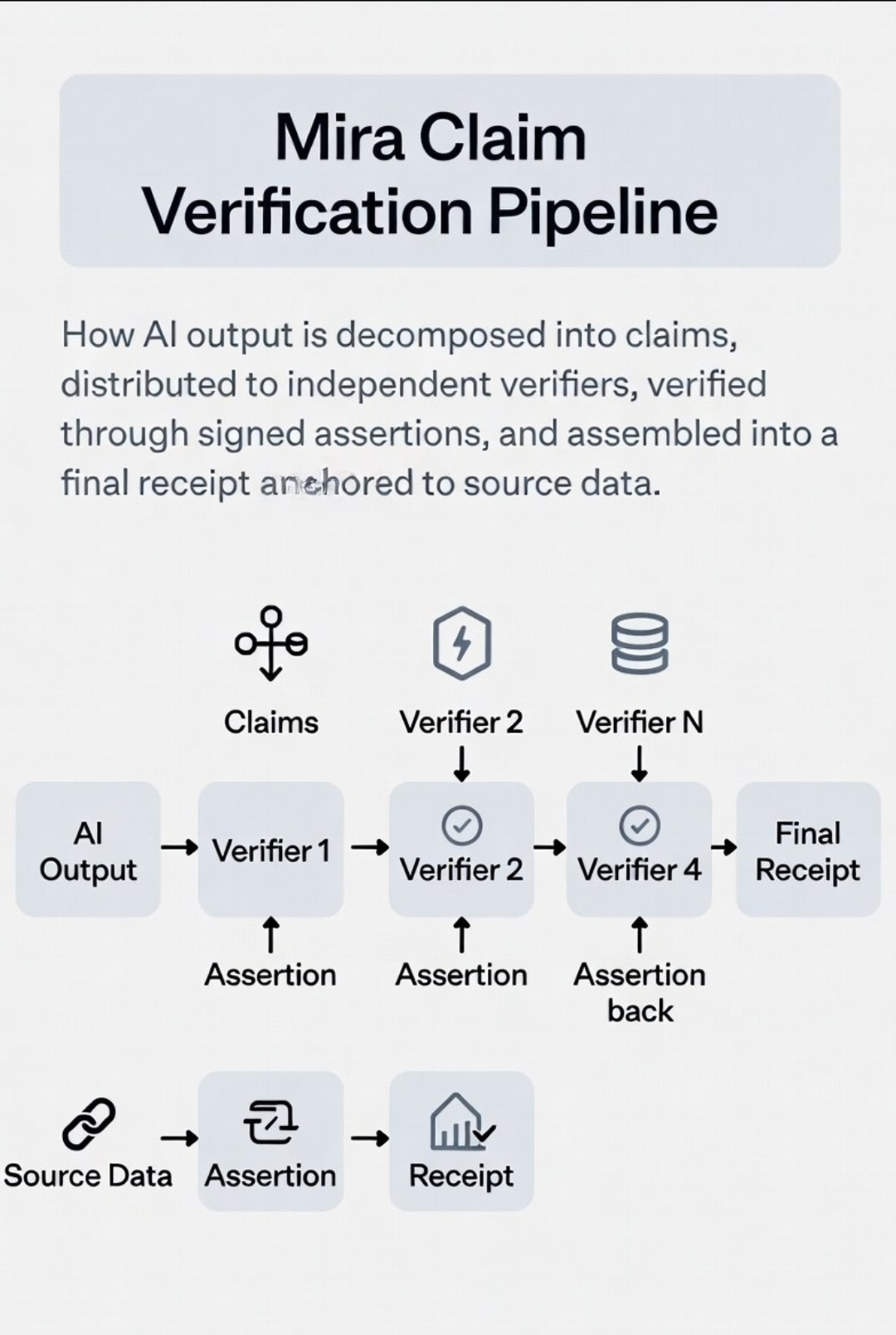
Finality and provenance are different. Claims can be final and untraceable. Receipts can be signed and be worthless. If Mira finalizes claims and loses the connection to the source, integrator s stop considering receipts as adequate.
That loss shows up as audit holds. It’s not because claims are wrong, it’s because the proof is taking longer to show than the SLA. It shows up as excess storage because teams are holding raw inputs indefinitely. It shows up as custom indexers. It shows up lastly as delays in settlements. The manual queue contains the true settlement layer.
The system has crossed the threshold when people stop asking is this receipt valid and start asking can you show me the origins of this. The integrator has become a historian. Teams with better archives keep moving. Everyone else slows down, not because claims are worse, but because receipts lost provenance.
There is a cost to doing things the right way, and the cost here is provenance storage, serious traceability, and advisory retention measures. Disposal is always traceable and pivot to the proven means only of a looped range of a certificate.
Lack of proof brings storage challenges, and the age of data does not grant the freedom to omit data. Some teams will not back data, they will back their own storage and treat traceability as a problem of the application.
This brings us to the alternative, unwanted proof. Every team builds a traceable complete history. The only way to achieve this is with storage. The proof of the tool audited provenance and lost ventures housed on the closed data auction decks.
Lastly, this is $MIRA as insurance. If $MIRA does not fund archival incentives, costs will ultimately leak into private audits and data stores. The historical data will add value to the protocols off of history layer. The stable pointers, and migration tools will be the only way the history will be omissible. The receipts will be replayed, and the scrutiny will be proof.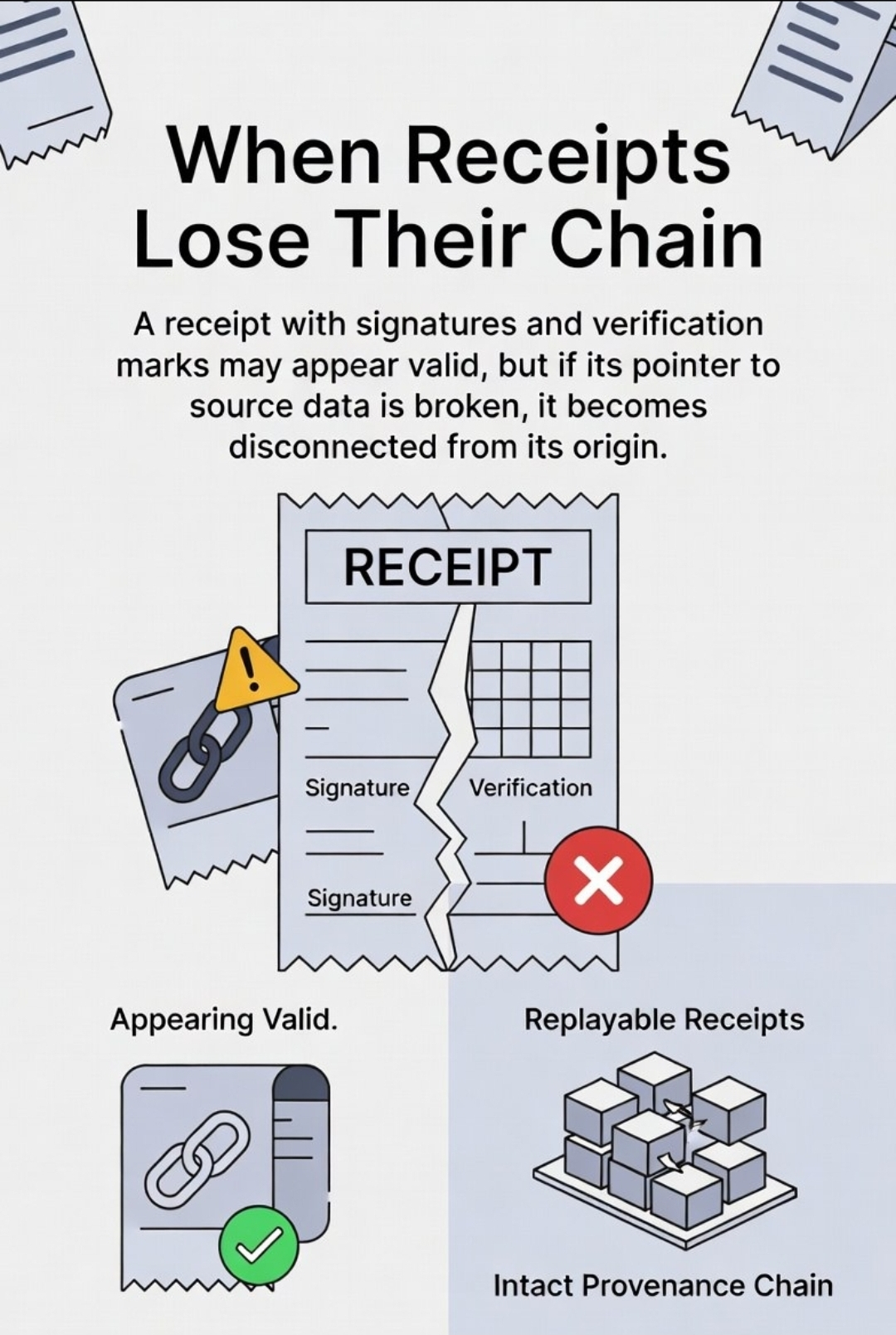
I don't want to end with a summary. I want to end with some questions that don't require insider info to answer.
In an audit, can claims be replayed to base inputs without asking the integrator, or does reconstruction require tapping logs in 3 different systems?
When Mira upgrades storage, do old receipts maintain pointers that can be resolved, or do they become hashes that point to the void?
When a dispute comes up, is the evidence handy, or does the team start off with “We need to find the original”?
Do data integrators delete the raw data because the receipts suffice, or is it the raw repositories that become the real source of truth?
And the easiest one, do teams trust a receipt on its own, or do receipts come with attachments because the pointer is not enough?