@Mira - Trust Layer of AI #Mira $MIRA
The certificate sealed before the newer checkpoint ever touched the claim.
I saw it in Mira's audit trail the next morning.
The earlier round was already closed. Fragment checks passed. Evidence paths matched what that Mira's validator mesh considered sufficient at the time. Stake weight attached. Certificate tuple settled into the consensus record. Clean finish. Done.
Nothing looked wrong.
That was yesterday's mesh. Anyways.
By evening one of the validator models on Mira network rotated to a newer checkpoint built on an updated consensus-validated dataset. Same architecture. Same job. Different idea of where enough evidence stops.
checkpoint_id: changed
validator_set_id: rotated
The old certificate stayed where it was.
Closed round. Finished proof.
The models didn't stay put.
I ran a near-identical request through Mira again the next morning. Same claim shape. Same factual contour. Claim decomposition split it the usual way... fragments minted, evidence hashes attached, distributed validation starting across the node set.
Normal start.
Then the familiar fragment hit the evidence branch.
Not the same wording. Close enough.
The previous validator mesh had taken the shorter route through the citation chain and sealed it. This newer checkpoint didn't. It walked. One level deeper. Found a revised version of the supporting dataset. Slowed down. The first weight came in later than it should have. The second validator took a different route entirely.
The old certificate was still sitting in Mira’s ledger with full proof attached, already usable by anything downstream that wanted a certified reference.
The new round was still deciding how much work the same claim deserved.
Same fragment surface.
Different validator behavior.
I kept the old certificate open in one pane and the live verification trace in the other.
Old path: shorter citation walk. Certificate sealed.
New path: deeper branch. Wider evidence graph. Weight attaching slower.
The claim still looked defensible.
The path didn't.
And that mattered because the old certificate was already the one downstream had cached.
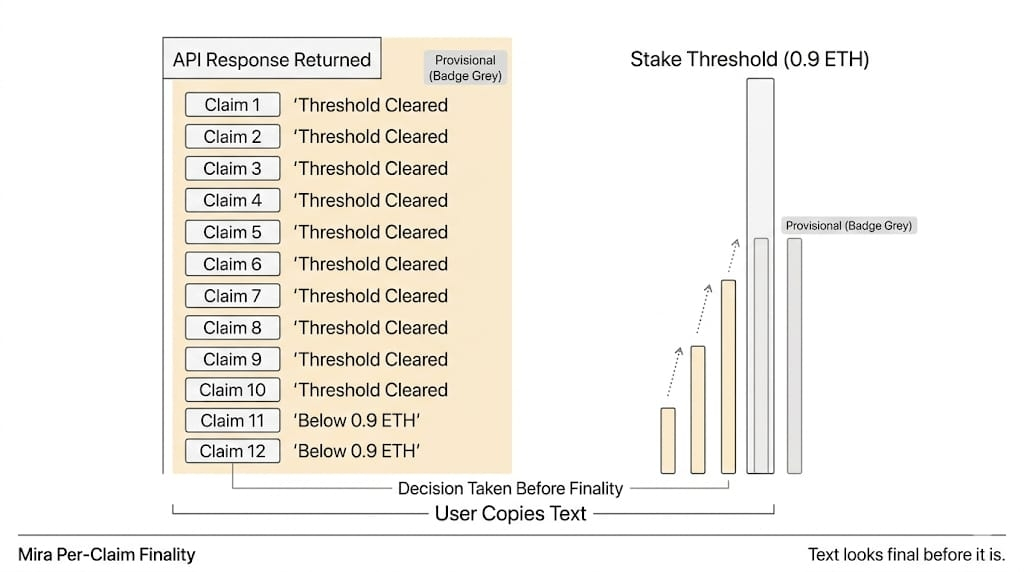
Downstream systems do not read "validator hesitation.' They read the certificate hash already sitting in the audit layer. If the old proof exists, it gets reused. Cached. Anchored into systems that will never rerun the whole mesh just because a checkpoint changed overnight.
Old proof versus new reasoning.
That was the split.
The old certificate remained fully valid while the newer validator mesh on Mira trustless consensus was already taking a different route to the same answer. If the next round had drifted harder, Mira would not have revised the earlier proof. It would have kept both states there... one sealed under the old validator set, one reached differently under the new one.
The ledger remembers the mesh that existed yesterday.
Today’s mesh has to live beside it.
I kept the traces open longer than I meant to. The newer checkpoint widened the evidence graph again. One validator attached weight. Another held back. Not rejection. Not even a clean split. Just enough drag to show the reasoning path had changed.
The earlier certificate didn't move.
It can't.
Once Mira seals fragment certificates into the consensus record, they become permanent references for anything downstream that trusts the audit layer. Checkpoints can move after that. Datasets can shift. Distributed validation can learn a slower, wider, stricter route through the same fragment.
The old certificate still resolves first.
If an integration already pinned the older certificate hash, it keeps using it. It doesn’t care that the newer validator mesh would now take a different path. It asked Mira for certified truth, got one, and moved on.
The newer round eventually converged.
Still valid.
Still certifiable.
Different reasoning trace.
I checked the earlier proof again anyway, like it might have updated itself while I was looking away.
Same certificate. Same validator set. Same preserved path.
Finished.
Another request has already entered the mesh now. Mira's Claim decomposition cut it clean. Evidence hashes are forming. The newer checkpoint is moving through the citation graph again, slower than the one that sealed yesterday’s proof.
The old certificate is still there.
Downstream still hits the old cert hash first.

