The quickest way to destroy a verification system is simple: slap a Verified tag on something that hasn’t actually been verified.
And it happens constantly. Not out of malice. It’s just how teams think. UX wants things to feel instant. Product wants friction gone. Developers see a smooth 200 OK response and their brain quietly checks the box: done.
That mindset works when you’re displaying a profile photo.
It absolutely doesn’t work when your entire value proposition is built on shared truth and distributed agreement.
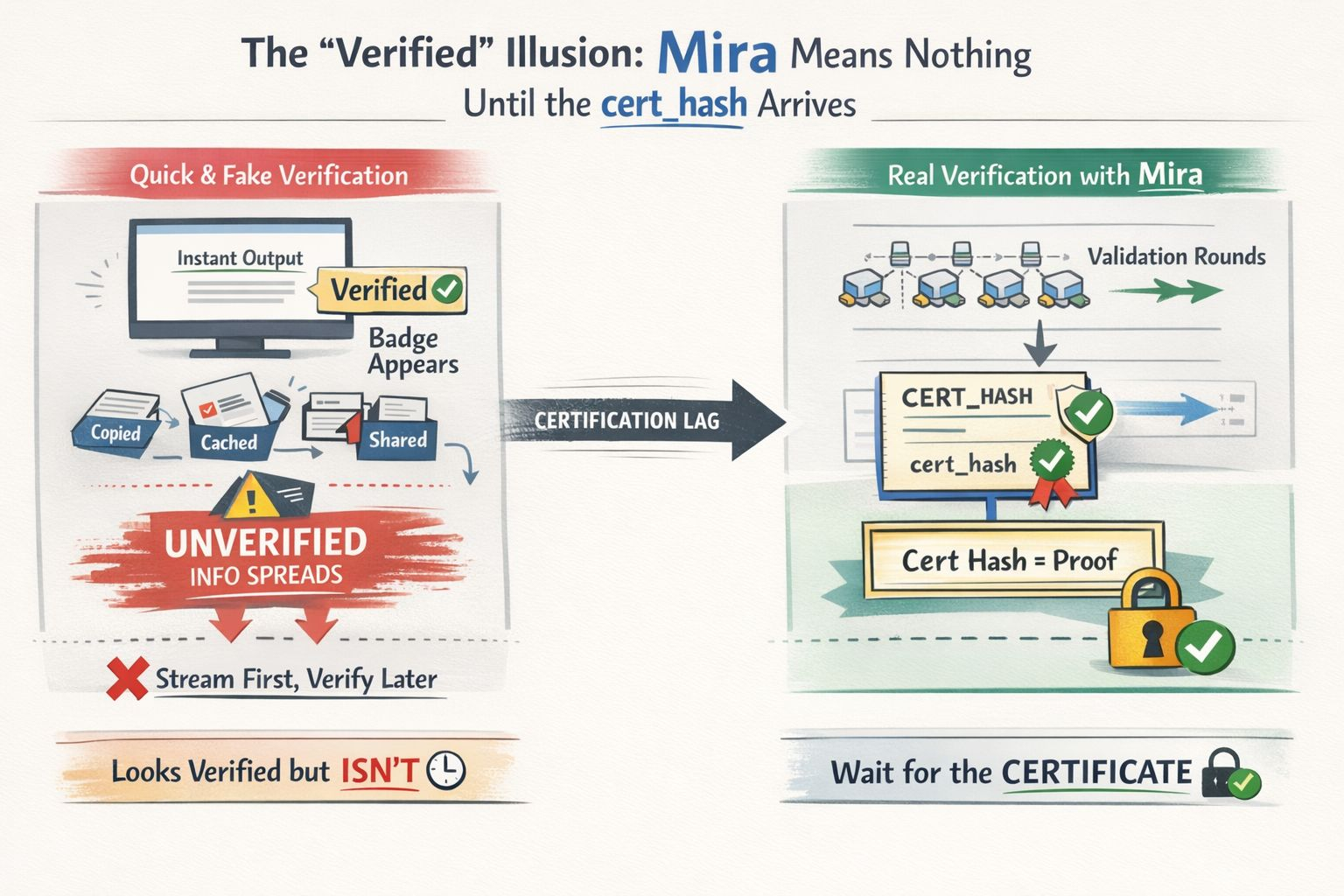
This is the uncomfortable friction Mira brings to the surface. Interfaces operate in milliseconds. Real verification doesn’t. It takes rounds, checks, confirmations. If you chase speed while telling yourself you’re protecting integrity, you end up creating something worse than slow or wrong. You create a system that looks fast, sounds confident, and stamps “verified” on content that hasn’t actually earned it.
At that point, you’re not really offering verification anymore. You’re offering presentation. A polished look. A feeling.
What Mira seems to insist on is simple but strict: “Verified” only has weight if it’s tied to actual agreement across the network. And that agreement isn’t some abstract mood. It’s recorded in something concrete — a cryptographic certificate, a cert_hash. That’s the piece you can carry around as proof that the output passed through the system, reached the required threshold, and was finalized properly.
Without that anchor, the word “verified” is just styling.
The flow itself is logical when you slow down and look at it. You don’t treat an answer like one giant block of text. You break it apart into clear claims or fragments. Each fragment gets its own identity — fragment IDs, evidence hashes — so you’re not approving a whole paragraph blindly. You’re checking individual statements. Different validator nodes, running different models, review those fragments independently and submit their results. When a supermajority is reached, the network generates a cryptographic certificate.
That certificate isn’t a side detail.
It’s the actual product.
That’s the piece an auditor can actually follow. It’s what a regulator can reference without guessing. It’s what a risk team can file away and pull up months later if someone asks hard questions. That’s where the word “verified” starts to carry real legal and operational weight. Not in how fast the API responded. Not in a shiny badge in the corner. Not even in the vague claim that “multiple models checked this.”
The cert_hash is the receipt.
And the mistake I see over and over again looks like this: stream now, verify later.
Developers push provisional output instantly because people hate waiting. The interface flashes a reassuring badge because it feels safer that way. Meanwhile, the actual certification process runs somewhere in the background, trying to catch up. Everyone convinces themselves it’s acceptable because, technically, the certificate will show up eventually.
The real harm lives in that space in between.
While everyone is waiting for the formal verification to finish, the unverified version is already out in the world. It gets copied into emails, saved in screenshots, stored in caches, pushed into other tools, maybe even used to make decisions. Most people will remember seeing the badge. They won’t remember whether it was provisional. And once that response starts flowing through an actual workflow, your so-called verification layer turns into something cosmetic — added after the fact, too late to matter.
It becomes even messier once caching is involved.
If provisional responses are cached with a TTL, and the system produces slightly different wording on separate requests, you can suddenly have multiple versions floating around. None of them tied to a cert hash. At that point, reproducibility is gone. Accountability is shaky. And when someone asks a simple question — “Which exact output was verified?” — you don’t have a clean answer. Because you allowed unverified variations to become the version people actually used.
This isn’t really a flaw in Mira. It’s a failure in how people assume it works.
Mira is built around consensus-backed verification. But if you plug it in like any other speedy API and treat a clean HTTP response as proof of verification, you’ve effectively removed the guarantee and kept the logo.
The solution isn’t flashy. It’s actually pretty dull — but it’s the entire point: the badge should only appear once there’s a certificate.
No cert_hash? Then it isn’t verified. Call it pending. Call it provisional. Call it a draft. But don’t label it verified. The moment you blur that line, you start eroding the very trust you’re claiming to establish.
It also forces you to separate two things people love to merge: speed and certainty. Yes, users can get quick output. That’s fine. But the interface has to be truthful about what that speed represents. Fast doesn’t mean proven. And if you want that badge to stand for real integrity, you have to accept the tradeoff — waiting for finalization before you stamp it.
If you actually want this to hold up in serious environments — audits, compliance checks, liability discussions — then the certificate can’t stay buried in the backend. It has to be visible. It has to ship with the output itself. The cert_hash should move alongside the verified claims so anyone downstream can trace the path and see exactly what was confirmed.
That’s the mindset shift Mira quietly demands from teams. Verification isn’t a background polish you apply at the end. It’s the deliverable. The certificate is the point where the system earns the right to say, “This wasn’t just produced. It was examined.”
In Mira’s framework, “usable truth” follows one strict rule:
you wait for the certificate.$MIRA @Mira - Trust Layer of AI #Mira