There is a moment every developer eventually faces when building on AI infrastructure. The API responds with 200 OK, the interface renders a confident answer, and everything appears to be working perfectly. On the surface, the system looks successful.
But the truth is more complicated.
Behind that smooth response, the real verification process may still be unfolding. In modern distributed verification systems like Mira Network, validation is not a single instant action. Instead, it is a structured consensus process where outputs are broken into individual claims, examined by multiple independent validator models, and tested against evidence before any final verification certificate is produced.
This creates a quiet but critical tension between speed and certainty.
User interfaces operate in milliseconds. Distributed consensus operates in rounds. When developers prioritize responsiveness and display results before verification has fully completed, the system risks presenting something that looks verified but has not yet earned that status.
In Mira’s architecture, the real proof is not the API response. It is the cert_hash — the cryptographic certificate that anchors a specific output to a completed consensus round. That certificate is what auditors can trace, regulators can inspect, and systems can rely on with confidence.
Without that certificate, a “verified” badge is just decoration.
The problem appears small at first. Developers often stream provisional responses to keep applications feeling fast, assuming the verification layer will catch up moments later. But users do not wait for certificates. They copy results, forward them to colleagues, and integrate them into decisions immediately. By the time verification finalizes, the provisional information may already be circulating.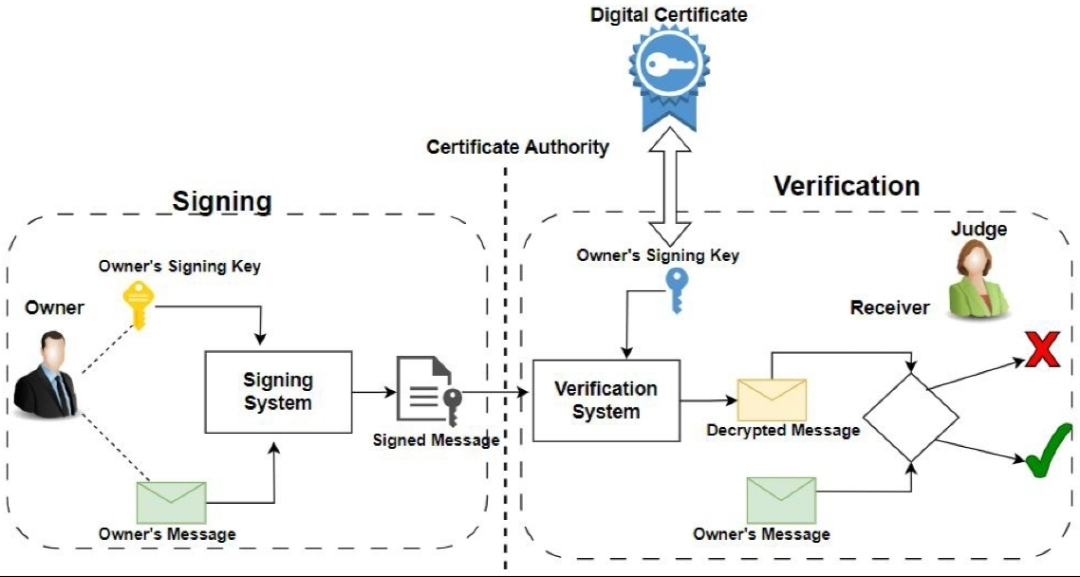
Caching introduces an even deeper complication. When responses are cached before verification completes, multiple slightly different provisional outputs can exist simultaneously. Without certificate hashes to anchor each one, tracing which answer was actually verified becomes nearly impossible.
This is not a flaw in Mira Network itself. The system clearly defines verification as the moment consensus produces a certificate. The issue arises when integrations blur that distinction and treat API success as verification success.
In reality, they represent two very different things.
An API response tells you a request finished.
A certificate tells you the answer survived scrutiny.
The lesson extends beyond any single protocol. Infrastructure designed for trust only works when downstream systems respect the moment that trust is actually established. Rendering results before verification completes is like settling a financial trade before settlement confirmation arrives.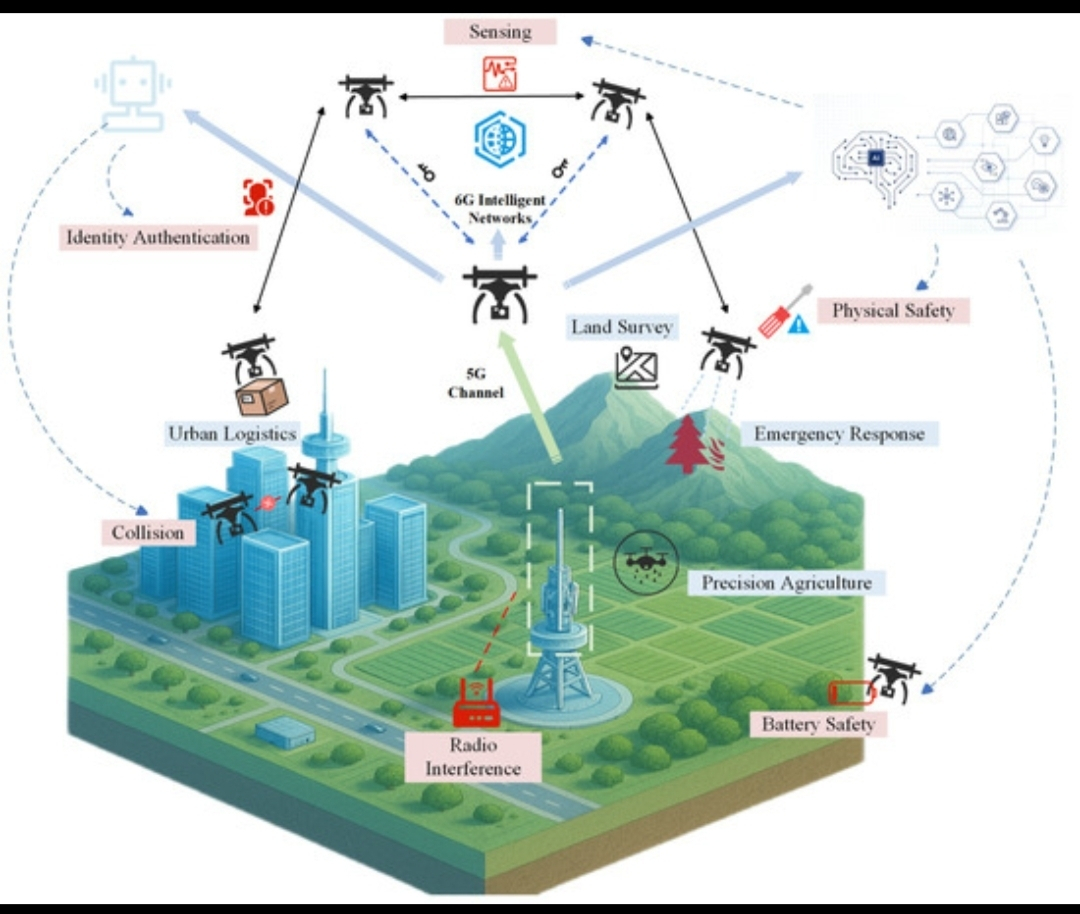
Technically, the solution is simple:
applications should only display verification badges once the cert_hash is returned, avoid caching provisional outputs, and expose certificates alongside verified claims.
But the deeper change is philosophical.
Developers must recognize that speed and assurance are not the same metric. One improves user experience. The other protects truth.
When building systems meant to verify reality, the badge should measure integrity — not latency.
Because in verification systems, the real product is not the answer.
It is the certificate that proves the answer survived consensus.