Introduction
Blockchain has completely changed how we think about digital infrastructure,letting us build transparent and decentralized systems.But privacy?That’s always been tricky.Most blockchains make every transaction visible to everyone,so keeping anything truly confidential isn’t easy even as businesses want both transparency and privacy in their operations.
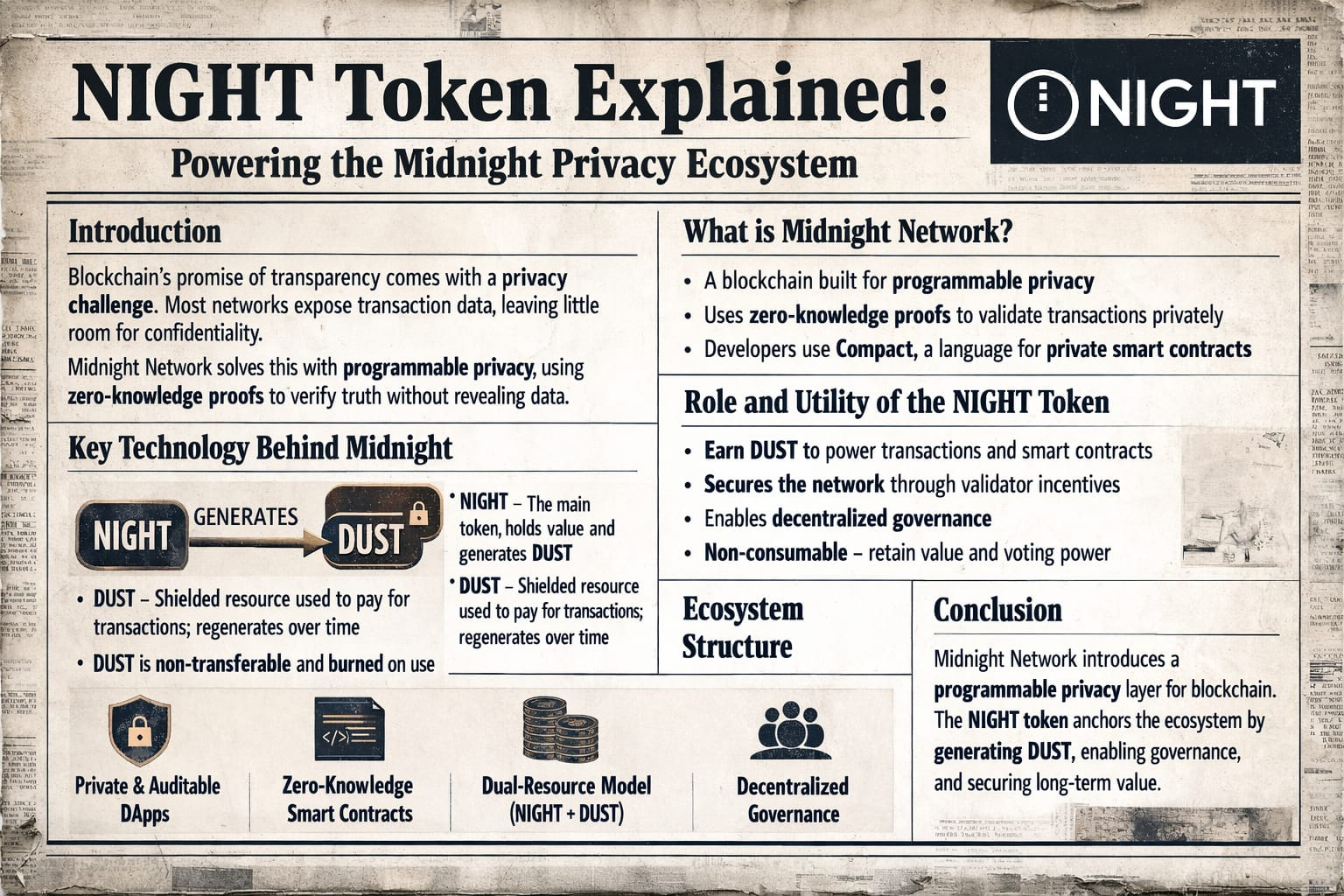
Midnight Network takes on this tension head on.It blends advanced cryptography with real,on chain verification.Instead of dumping every detail onto a public ledger,Midnight lets the network prove something is true,without exposing the sensitive info behind it.Privacy and transparency,working side by side.
And at the core?The NIGHT Token.It’s not just another transactional coin.NIGHT anchors the whole system,coordinating everything from smart contract operation to network governance.It’s the backbone for privacy enabled contracts and apps across Midnight.
So if you want to understand how programmable privacy can fit inside a decentralized system,you need to look at what Midnight builds and the essential role NIGHT plays running the show.
What is Midnight Network?
Midnight Network is all about programmable privacy using cutting edge cryptographic tools to verify operations without exposing confidential data.The star here is zero knowledge proofs:they let one party prove something’s true,while keeping the raw evidence hidden.
This is a big shift from older blockchains,where every transaction’s out in the open.With Midnight,you get a balanced structure:sensitive data stays private,yet every action remains verifiable.Apps built for Midnight can prove compliance or correctness without exposing user data.
Developers don’t have to wrestle with dense cryptography themselves either.Midnight offers Compact,its purpose built programming language for zero knowledge smart contracts.With it,coders bring privacy features into their decentralized applications without managing complex cryptographic logic on their own.
Key Technology Behind Midnight
Midnight stands out with a two part model for how resources move and get used on the network.Instead of having users spend a single token for every action,Midnight uses two connected parts,each with its own job.
First,there’s NIGHT.It’s the public token of value on the network.Second,there’s DUST a shielded resource that actually pays for running transactions and smart contracts.
Here’s how it works:just holding NIGHT steadily generates DUST for you,like a renewable resource.When you use DUST for running network operations,it slowly refills based on how much NIGHT you hold.
This design has a few clear upsides.Users can predict how much network activity they’ll be able to carry out,since DUST keeps regenerating.You don’t need to keep buying more tokens over and over.Separating NIGHT and DUST also guards overall economic value from being tied up in operating expenses.
Another important point DUST can’t be traded or transferred.It’s shielded and only exists to be burned on activity.That prevents gaming the system and keeps economic incentives in line,all while reinforcing the privacy model.
Role and Utility of the NIGHT Token
NIGHT does a lot of heavy lifting for the Midnight ecosystem.First,it’s how users get DUST,which runs smart contracts and transactions.NIGHT itself isn’t burned or spent for operations it simply enables ongoing access. So as long as users hold NIGHT,they have a renewable resource powering their activities without losing their core holdings.
On top of that,NIGHT supports network security.Validators and consensus mechanisms use it for incentives and to keep the network performing smoothly and safely.
NIGHT also brings governance into the picture.Holders can vote on changes,upgrades,and the overall direction of Midnight.This keeps decision making in the hands of real participants,enriching community involvement.
Most important:since NIGHT isn’t consumed,you don’t give up your long term value or voice in the community just to use the network.
Ecosystem Structure
Midnight’s ecosystem is built to host decentralized apps that need both privacy and auditability.Zero knowledge smart contracts guard sensitive computations,and users can selectively prove compliance without leaking data.
The two token DUST and NIGHT model keeps economic ownership and network resources separate,so transactions remain efficient and predictable.Developer tools like Compact make these advanced features actually accessible,lowering technical barriers to entry.
With all these pieces in place,developers and users can interact securely while keeping their information under control.
Conclusion
Midnight Network brings something new to blockchain privacy transparent processes,but with confidential data handling.Zero knowledge smart contracts and the dual-resource (NIGHT and DUST) model keep network costs and underlying value clearly separated.
NIGHT remains the central player,continually generating the DUST resource for operations,backing governance,and buttressing infrastructure stability.
By joining privacy and transparency in a programmable framework,Midnight shows a path forward for blockchain apps.As decentralized tech moves ahead, solutions that blend cryptography,clever economic mechanisms,and developer friendly tools will become increasingly influential and Midnight is clearly betting on that future.