Conversations about blockchain infrastructure often revolve around familiar ideas: decentralization, trust minimization, and immutable ledgers. These principles have shaped the architecture of most existing networks. Yet when we begin thinking about systems that must coordinate machines, robots, or autonomous agents in the physical world, some of those assumptions start to look incomplete. The design challenges shift from simply recording transactions to verifying actions, coordinating machines, and securing infrastructure that operates continuously in unpredictable environments.
This is where the design philosophy behind Fabric Protocol becomes particularly interesting. Instead of treating validators as fixed participants within a static network, the protocol explores the idea that trust should be dynamic, constantly reshaped by the network itself. The idea sounds simple, but its implications for security and infrastructure are profound.
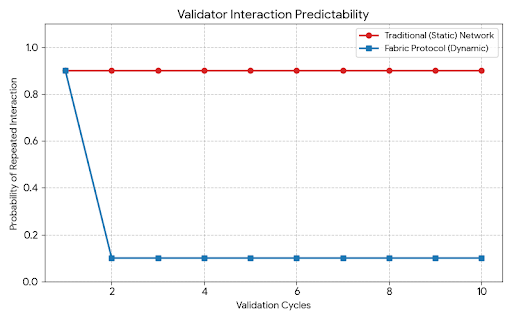
Traditional blockchain networks generally rely on a relatively stable set of validators. Whether in proof-of-stake or delegated systems, a subset of participants repeatedly performs the same role: proposing blocks, validating transactions, and maintaining consensus. Over time, these participants become well known within the system. Their identities, roles, and operational patterns become predictable.
Predictability, however, is not always desirable in a system designed to resist manipulation.
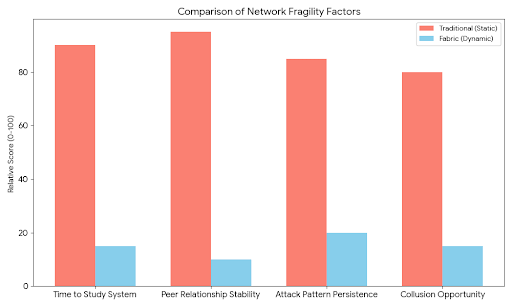
When validators remain static, adversaries gain time. Time to study the system. Time to model validator behavior. Time to plan attacks that exploit known network relationships or repeated communication pathways. Even if the validator set is decentralized, long-term stability creates patterns. Patterns, in security design, often become the weakest point.
Fabric Protocol approaches this challenge from a different perspective. Rather than accepting static validator relationships as a necessary trade-off, it treats them as a design problem that can be actively solved. Validators within the network are not fixed partners who repeatedly communicate with the same peers. Instead, they are continuously rotated through different interaction groups and verification pathways.
The important detail here is not simply rotation, but unpredictability.
In Fabric’s architecture, validation relationships are intentionally reshuffled over time so that the same contacts are rarely repeated. A validator that verifies a particular event or action in one cycle will likely interact with a completely different set of peers in the next. The network continually re-weaves its own trust fabric, preventing long-term dependency between specific participants.
This design introduces an important security property: adversaries cannot easily predict who will verify what.
For networks designed to support autonomous machines or robotic systems, this becomes even more valuable. Imagine a distributed infrastructure where robots, sensors, and autonomous services produce data that must be verified before it becomes part of the shared state. In such a system, the risk is not only financial manipulation but also the injection of false real-world signals. If verification pathways remain stable, attackers may eventually identify where influence can be applied.
By forcing validators to constantly interact with new peers, Fabric reduces the possibility of coordinated manipulation. No single group can reliably maintain influence over a particular verification process because the participants involved in each round are always changing.
The architecture begins to resemble a constantly shifting mesh rather than a rigid validator hierarchy.
Another interesting aspect of this design is how it reframes the concept of infrastructure. In many blockchains, infrastructure is built around persistent nodes performing consistent roles. Fabric instead leans toward the idea of shared infrastructure that behaves more like a distributed service layer. Validators act less like permanent authorities and more like temporary participants in verification cycles.
This temporary role assignment changes the incentives and operational dynamics of the network. Validators cannot rely on predictable relationships to optimize their strategies. Instead, they must behave correctly within a constantly evolving environment where reputation and reliability are evaluated across many different interaction contexts.
From a security standpoint, this reduces the risk of long-term collusion. In systems where the same validators repeatedly work together, subtle coordination can occur without immediate detection. Over time, small cooperative behaviors may accumulate into larger structural risks.
Dynamic validator rotation disrupts this possibility.
It ensures that cooperation between malicious actors becomes far more difficult because they cannot reliably encounter the same partners across validation cycles. Even if adversaries control several nodes, the probability that those nodes consistently converge in the same verification groups becomes statistically small.
This concept also aligns with a broader shift in how blockchain infrastructure may evolve to support machine-driven systems. As networks begin interacting with robotics, AI services, and automated logistics platforms, the integrity of real-world data becomes a core challenge. Verification cannot rely purely on cryptographic signatures; it must also account for the trustworthiness of the entities performing validation.
By distributing verification responsibilities across constantly changing participants, Fabric creates a system where trust emerges from diversity rather than permanence.
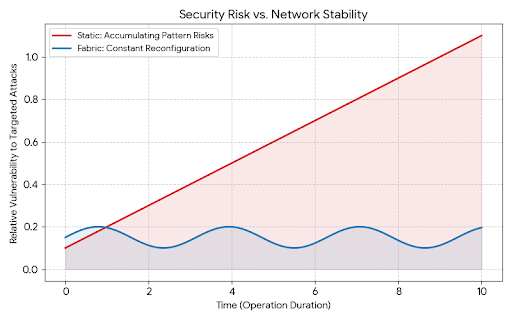
The design philosophy here is subtle but significant. Instead of assuming that a stable validator set is inherently secure, the protocol assumes that long-term stability introduces hidden risks. The solution is not simply increasing decentralization but introducing controlled unpredictability into the system itself.
Security in this model becomes a property of motion rather than structure.
Networks are often described as “secure by design,” but Fabric suggests that security may also come from continual reconfiguration. The system protects itself not by locking roles into place but by ensuring that no role remains static for long.
This approach may feel unfamiliar to those accustomed to conventional blockchain architectures, yet it mirrors patterns seen in other resilient systems. Biological networks, distributed computing clusters, and even certain cybersecurity frameworks often rely on dynamic reallocation of tasks to prevent predictable attack surfaces.
Applied to blockchain infrastructure, the result is a network that behaves less like a static ledger and more like a living system.
For autonomous machines and robotic networks, this kind of adaptability may become essential. Robots operating within shared infrastructure must rely on verification systems that cannot be easily compromised or manipulated over time. A validator architecture that constantly refreshes its relationships offers a path toward that resilience.
Fabric Protocol’s ideas suggest that the future of blockchain infrastructure may not simply involve faster transactions or larger validator sets. Instead, it may require rethinking how trust is constructed within the network itself.
If validators are never static, if verification pathways are continuously reshaped, and if participants rarely encounter the same contacts twice, the network becomes far harder to predict and therefore far harder to control.
In a world where machines, data, and infrastructure are increasingly intertwined, unpredictability might turn out to be one of the most valuable forms of security a protocol can offer.
#ROBO @Fabric Foundation $ROBO
