 1. Introduction: The "Privacy vs. Compliance" Paradox
1. Introduction: The "Privacy vs. Compliance" Paradox
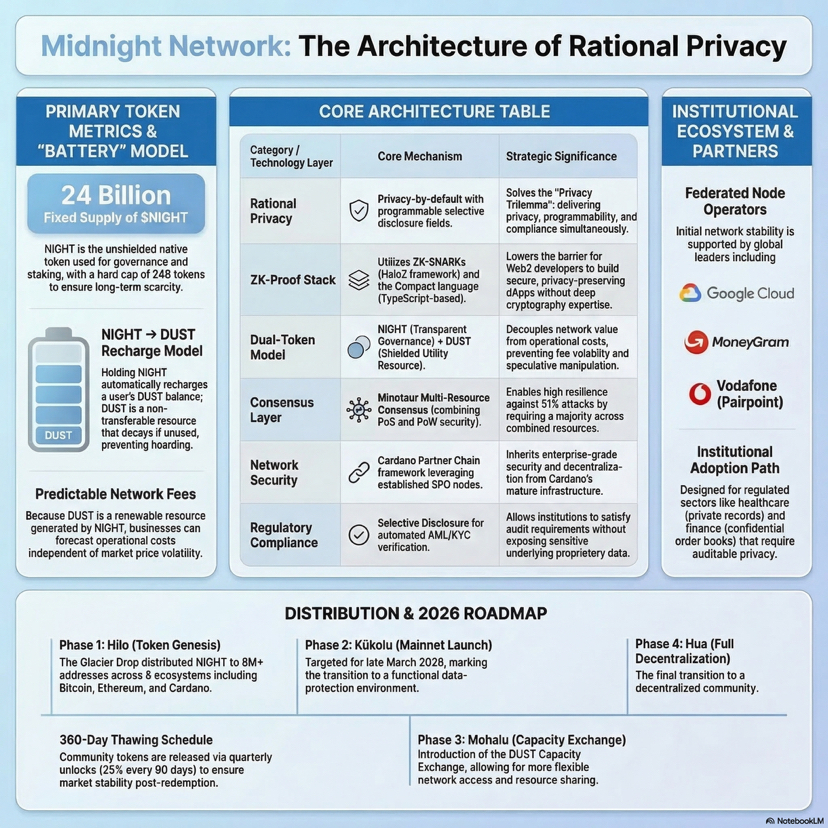
In the evolution of decentralized systems, a critical friction point has emerged between the right to individual privacy and the legal mandates of global financial markets. While early privacy coins prioritized absolute anonymity to prevent surveillance, this "unconditional" approach fundamentally clashes with Anti-Money Laundering (AML) and Know Your Customer (KYC) requirements. Consequently, such assets often face delisting and institutional exclusion under frameworks like the EU’s MiCA (Markets in Crypto-Assets) regulation.
To bridge this gap, we must move toward a model of Rational Privacy.
Rational Privacy is a programmable, data-protection paradigm that provides default confidentiality for users and enterprises while enabling selective, auditable disclosure to satisfy specific regulatory or business requirements.
This shift represents the "Fourth Generation" of blockchain, moving beyond mere smart contracts and scalability to address the final hurdle: secure, compliant data execution.
--------------------------------------------------------------------------------
2. Anonymity vs. Auditable Privacy: A Comparative Analysis
For enterprise leaders, the "So what?" is clear: Midnight is not a "dark coin" meant to circumvent the law; it is a "data protection chain" designed to satisfy it. Unlike unconditional models that offer a "trust me bro" approach to regulators, Midnight uses cryptographic proofs to verify compliance.
Feature
Unconditional Model (e.g., Monero)
Rational Model (Midnight)
Primary Goal
Unconditional Anonymity
Programmatically Conditional Privacy
Default State
Fully concealed; untraceable by design
Private by default; programmable for audit
Legal Compliance
High risk of delisting (MiCA/AML bans)
Designed for institutional/regulatory alignment
Primary User
Individuals avoiding all surveillance
Regulated institutions, Enterprises, DeFi
Disclosure
Viewkeys (Complex selective decryption)
Selective Disclosure via ZK-Proofs
--------------------------------------------------------------------------------
3. The Cryptographic Secret Sauce: Kachina, ZK-Proofs, and "Compact"
To achieve auditable privacy without leaking raw data, Midnight utilizes a sophisticated technology stack. While older systems rely on "viewkeys" to decrypt transaction history, Midnight uses Zero-Knowledge Proofs (ZK-proofs)—specifically zk-SNARKs—and the Kachina protocol.
Kachina Protocol: Manages "Private Shared State," allowing smart contracts to process confidential information without exposing it on the public ledger.
Compact: A TypeScript-based domain-specific language (DSL) that allows developers to write private smart contracts without needing a PhD in cryptography.
The 3-Step Logic of a ZK-Proof
Imagine needing to prove you are of legal age to enter a venue without showing your birth date, name, or address:
The Statement: You claim, "I am older than 18."
The Proof: You use a cryptographic "black box" (the ZK-proof) to check your ID and generate a mathematical certificate of validity.
The Verification: The bouncer (the blockchain) checks the certificate. The math proves you are over 18 without the bouncer ever seeing your personal data.
--------------------------------------------------------------------------------
4. The Engine of Midnight: The NIGHT/DUST Battery Model
Midnight operates on a "Dual-Token" model designed to ensure economic predictability—a vital requirement for regulated entities that cannot tolerate volatile "gas" fees.
The "Battery Recharge" Metaphor
NIGHT is the public utility token, while DUST is the shielded resource used for network fees. Holding NIGHT acts as a "Battery," automatically generating DUST.
NIGHT (Public Utility): 24 billion fixed supply. Used for staking, governance, and securing the network. It is unshielded and tradable on major exchanges.
DUST (Shielded Resource): A non-transferable resource generated by holding NIGHT. It is used to pay for transaction fees and dApp execution.
Feature
NIGHT Token
DUST Resource
Tradability
Publicly tradable (Binance, eToro, etc.)
Non-transferable; cannot be traded
Visibility
Unshielded; public transactions
Shielded; private operational resource
Supply
Fixed (24 Billion)
Infinite/Resource-based (NIGHT-recharged)
Economic Role
Investment, Staking, Governance
Predictable network capacity/gas fees
Insight: During the upcoming Mohalu phase, the network will introduce the DUST Capacity Exchange, allowing users to trade the right to network capacity even if they don't hold NIGHT.
--------------------------------------------------------------------------------
5. Institutional Validation: The Partner Chain Strategy
Midnight is not a sidechain; it is an independent Layer-1 Partner Chain that inherits its security from Cardano’s robust PoS ecosystem. It utilizes the Minotaur consensus protocol—a hybrid of Proof-of-Work (PoW) and Proof-of-Stake (PoS)—making it more resilient to fluctuations than pure PoW chains like Bitcoin.
This architectural stability has attracted a "Node Alliance" of global leaders:
Google Cloud: Provides massive compute for ZK-generation and utilizes Confidential Computing and Mandiantthreat monitoring to secure the network.
MoneyGram: Leveraging Midnight for cross-border remittances, solving the privacy-compliance tension in global payments.
Vodafone (Pairpoint): Focusing on the Economy of Things (IoT), allowing devices to exchange data and trade privately and securely.
eToro & Blockdaemon: Providing institutional-grade infrastructure and access for retail and professional traders.
--------------------------------------------------------------------------------
6. The Road to 2026: Roadmap and Redemption
The network is currently navigating its "Hawaiian Moon Cycle" phases toward full decentralization.
[x] Hilo Phase (Late 2025): Token launch and initial liquidity for NIGHT.
[x] Kūkolu Phase (Active): Stable mainnet conditions reached. Genesis block projected in ~90 days. Developers can now deploy real dApps using Compact.
[ ] Mohalu Phase (Q2 2026): Block production opens to community operators (SPOs); launch of the DUST Capacity Exchange.
[ ] Hua Phase (Q3 2026+): Multi-chain integration via LayerZero, positioning Midnight as a security tool for Ethereum and beyond.
The Glacier Drop and Thawing Process
To ensure sustainable growth, NIGHT tokens are distributed via the "Glacier Drop" and a 360-day thawing period:
Randomized Start: Each recipient is assigned a random start date between Dec 10, 2025, and early March 2026.
Quarterly Unlocks: 25% of the allocation unlocks every 90 days.
Grace Period: A final 90-day window following the 360-day thaw allows for final claims before the redemption portal closes.
--------------------------------------------------------------------------------
7. Summary Checklist: Is Midnight Right for Your Project?
If you must satisfy AML/KYC requirements while keeping proprietary client data off a public ledger, thenMidnight is your tool.
If you are a developer looking to build private apps using familiar tools (TypeScript/Compact) without specialized crypto-math knowledge, then Midnight is your tool.
If you require a predictable fee structure (Battery model) rather than volatile gas markets, then Midnight is your tool.
If your goal is absolute, unconditional anonymity that evades all forms of auditing or disclosure, then Midnight is not the tool for you.
If privacy chains cannot prove compliance, regulators will eventually remove them from the financial system. Midnight seems to be one of the few projects designing for that reality.
#night $NIGHT @MidnightNetwork
