I want to start by saying this is the kind of idea that quietly changes what we expect from technology. Midnight is a new kind of blockchain that was built so people and builders do not have to choose between useful apps and keeping certain data private. At its core Midnight aims to let apps prove things without revealing the private bits that make those things true. That sounds simple but it changes a lot. Instead of every action being visible to everyone, Midnight lets verification and privacy live together so wallets, contracts, and services can protect identities and business secrets while still being part of an open network. This is not about hiding things for the sake of secrecy. It is about giving people and projects control so they can decide what stays private and what is shown. The project’s own technical write ups and whitepaper explain this goal and the architecture behind it.
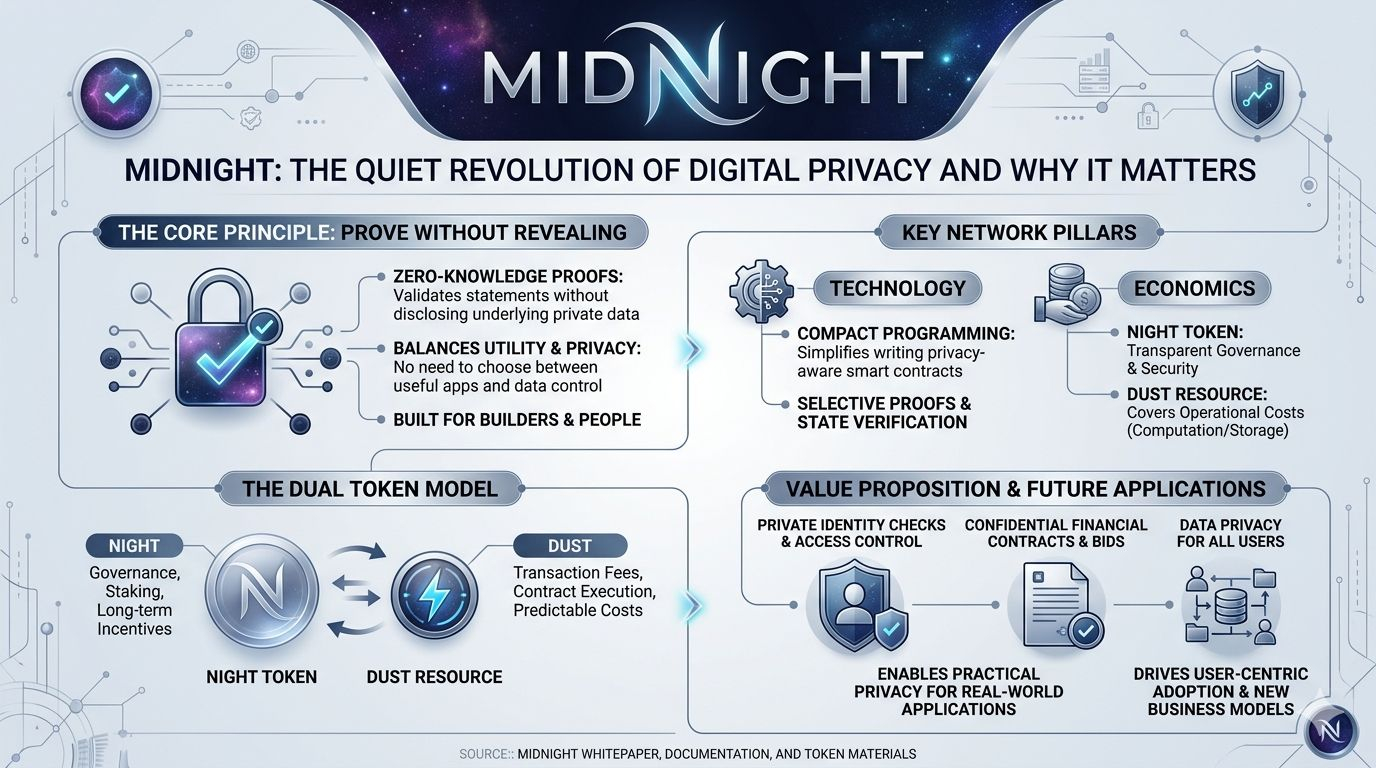
If you want to understand how Midnight actually does it, think of two parts working together. One part is the math that proves statements without showing the underlying data. Those proofs are the glue that keep privacy intact while letting others trust the outcome. The other part is the developer tooling and programming model that make writing these privacy aware apps sensible and productive. Midnight separates the contract logic from heavy cryptographic plumbing so that builders can write privacy aware code without becoming cryptography experts. They introduced a compact programming approach and developer docs to show how contracts should be designed for protected data. That way apps can request selective proofs, verify state, and let users reveal only what matters when they choose to. The network documentation and developer resources walk through these decisions and show how to build and test private smart contracts.
We’re also seeing a thoughtful economic design that helps the system work in practice. Midnight uses a native governance token called NIGHT and a separate network resource called DUST which is used to pay for computation and storage. NIGHT is meant to be transparent and tradable while DUST is the operational fuel that contracts consume. The separation makes it easier to run private operations without conflating governance and routine fees. In practice that means holders of NIGHT help secure and guide the network while DUST is generated or consumed as the network runs. Token papers and the project’s token pages explain the generation of DUST and how the NIGHT token ties into governance and incentives. These mechanics are meant to sustain developer activity and make sure the cost of privacy is predictable for users and services.
Why did Midnight appear now and where could it go next If you look at the ecosystem around blockchains you’ll see many powerful apps but also recurring complaints about leaking private information and business models that force transparency in ways companies and individuals do not want. Midnight tries to answer a clear need. It wants to enable practical privacy for real world uses such as private identity checks, sealed bids, confidential financial contracts, and access controlled data markets. If those use cases catch on we could see a wave of applications that offer new value because they protect user choices and proprietary data while still allowing verification and settlement on chain. That would attract businesses that need compliance and privacy and users who want control without losing convenience. Along the way the project can open up a different path for collectibles, games, and financial instruments where certain details remain private but outcomes remain provable. The project blog and community updates show examples and challenges for adoption which help paint a picture of possible next steps.
Talking about value flow makes this less abstract. Value moves through Midnight in familiar ways but with an extra privacy layer. People and services can interact with contracts that hide sensitive inputs but still update shared state. Fees are paid with the resource layer so costs are tied directly to network usage. Governance decisions and allocation of incentives are managed through the NIGHT token so the token economy steers long term choices. Developers and companies that build useful private apps will attract users who need those protections and that usage will generate the resource consumption that funds the network’s operations. Over time the ecosystem could build complementary services such as identity attestation, off chain data oracles that feed proofs, and permissions systems that let businesses run private liquidity pools or payroll or bidding systems in ways they could not before. If we’re careful about user experience and developer support this could shift where value is captured and how it is shared among builders, users, and token holders.
It is worth saying that this path is not free of friction. Privacy adds complexity for audits and for regulators who care about transparency in finance and commerce. Midnight’s approach is to keep the governance token transparent and to give tools for selective disclosure so that when a lawful need appears there are patterns to reveal the right information without tearing down the whole privacy model. The challenge will be making these patterns standard, auditable, and easy to use. We are likely to see slow and deliberate growth as wallets, libraries, and third party tools mature and as teams build clear examples where privacy is not just a feature but a requirement for the business case.

I’m excited by the human side of this story too because people and teams who care about privacy will finally have a practical platform to build on. They’re the ones who will show us the real possibilities. At first we’ll get niche apps that need confidential inputs. Then those apps will show broader audiences that you can get the benefits of public blockchains without giving up control over private details. That shift is not overnight but it is meaningful. If Midnight and its community keep delivering developer tools, clear docs, and real use cases we’re likely to see new categories of services and new business models that link privacy to value in honest ways.
To close this feels like the beginning of a new chapter rather than the final draft. Midnight gives builders a menu of technical choices for privacy and a token structure that separates governance from operational fuel. That combination matters because it lets teams design products that are legally compliant, technically private, and economically sensible all at once. We’re at a moment where privacy can become a practical part of the stack instead of an afterthought. If you build, invest, or just follow this space it is worth watching how projects that focus on selective proofs and developer experience grow into tools that everyday people and companies can rely on. The whitepaper, documentation, and token materials give a solid starting point for anyone who wants to explore more.
#night @MidnightNetwork $NIGHT #DUST
