I have spent years dissecting blockchain protocols, but my recent run-in with a smart contract on Midnight Network felt different. Usually, when you trigger a transaction, you expect the glass box effect where everything is visible, exposed, and archived. But as I watched a real-world transaction move through Midnight’s pipes, I realized I was not just looking at another privacy coin; I was looking at a total shift in how decentralized trust actually works.$NIGHT
The process started off deceptively simple. I fired off a transaction, the network hummed, and within seconds, I got the confirmation. In any other ecosystem, be it Bitcoin or Ethereum, this is where the curtain pulls back. You hop onto the explorer, check the addresses, and trace the data flow. But when I pulled up the Midnight ledger, the screen was effectively a ghost town. The confirmation was loud and clear, yet the data behind it was a total void. No input history. No trace of the logic used in the computation. The system was shouting success while keeping the actual how and what locked in a vault. This is the moment where traditional transparency dies and cryptographic certainty takes over.
What really caught my attention was the behavior of the validators. In a standard setup, nodes have to see the data to verify it. On Midnight, they were operating in the dark and that is the genius of it. I watched as nodes across the network reached a consensus on a proof they could not actually read in the traditional sense. They were not checking my data; they were checking the mathematical integrity of the proof I submitted. It is a high-stakes game of verification where the rules are absolute, but the secrets are kept.
You cannot talk about this network without looking at the NIGHT token. Most people treat native tokens as mere trading tickers, but here, $NIGHT is the literal fuel for this invisible machine. Without a massive incentive for validators to maintain this complex infrastructure, the whole thing would stall. NIGHT is not just a reward; it is the glue for the governance and the security that allows this level of privacy to even exist. It creates a balance where the network is incentivized to stay honest while keeping everyone else's business private.
The most striking realization came during a test of identity verification. Normally, proving you are eligible for something involves a messy exchange of documents and personal risk. On Midnight, the network confirmed the fact without ever touching the identity. This is the bridge we have been waiting for. Financial checks, secure contracts, and sensitive agreements can finally move onto the chain without the fear of a permanent data leak.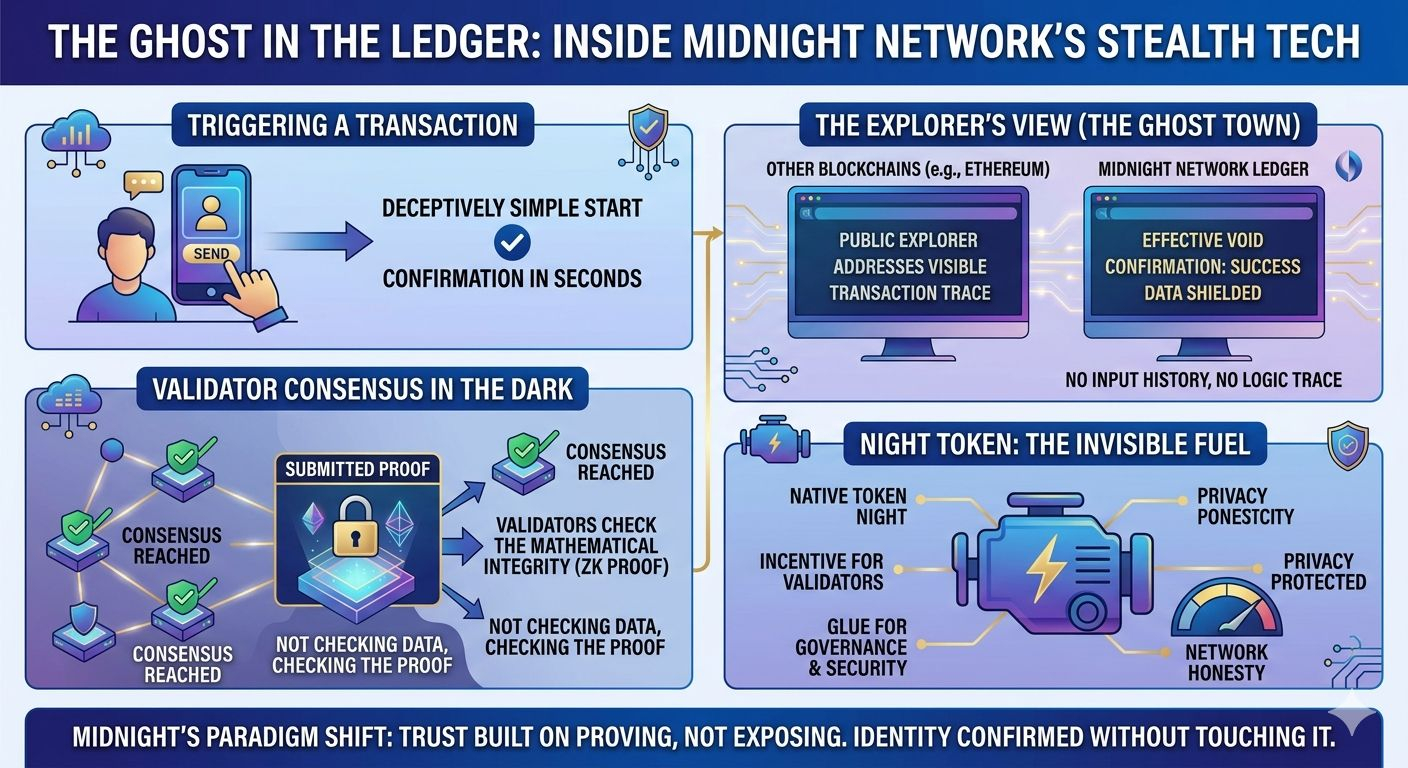
My takeaway? We have been trained to believe that if you cannot see the data, you cannot trust the result. Midnight flips that script. It proves that the strongest possible confirmation is not the one that exposes the secret but the one that protects it.