@MidnightNetwork #night $NIGHT

When you think about privacy in blockchain, the first image that comes to mind is usually one of total anonymity: users transacting without revealing anything about themselves. Midnight Network approaches privacy differently. It doesn’t just hide data for the sake of secrecy; it creates a system where transactions and interactions remain private but still accountable. This distinction is subtle but important. Midnight’s approach relies on zero-knowledge proofs, a cryptographic technique that allows one party to prove something is true without revealing the underlying details. In practice, this means a user can confirm a transaction is valid without exposing the amounts, counterparties, or other sensitive details.
Imagine a freelance platform built on Midnight. Two people agree on a service and a payment. Traditional blockchains would make this transaction publicly visible, revealing who paid whom and how much. On Midnight, the platform can verify that the payment is legitimate without exposing these numbers. The freelancer sees that they’ve been paid, and the system confirms the legitimacy to the platform, but outside observers cannot trace the flow. The same principle applies to more complex interactions, like decentralized lending or data-sharing agreements, where revealing too much could create risks.
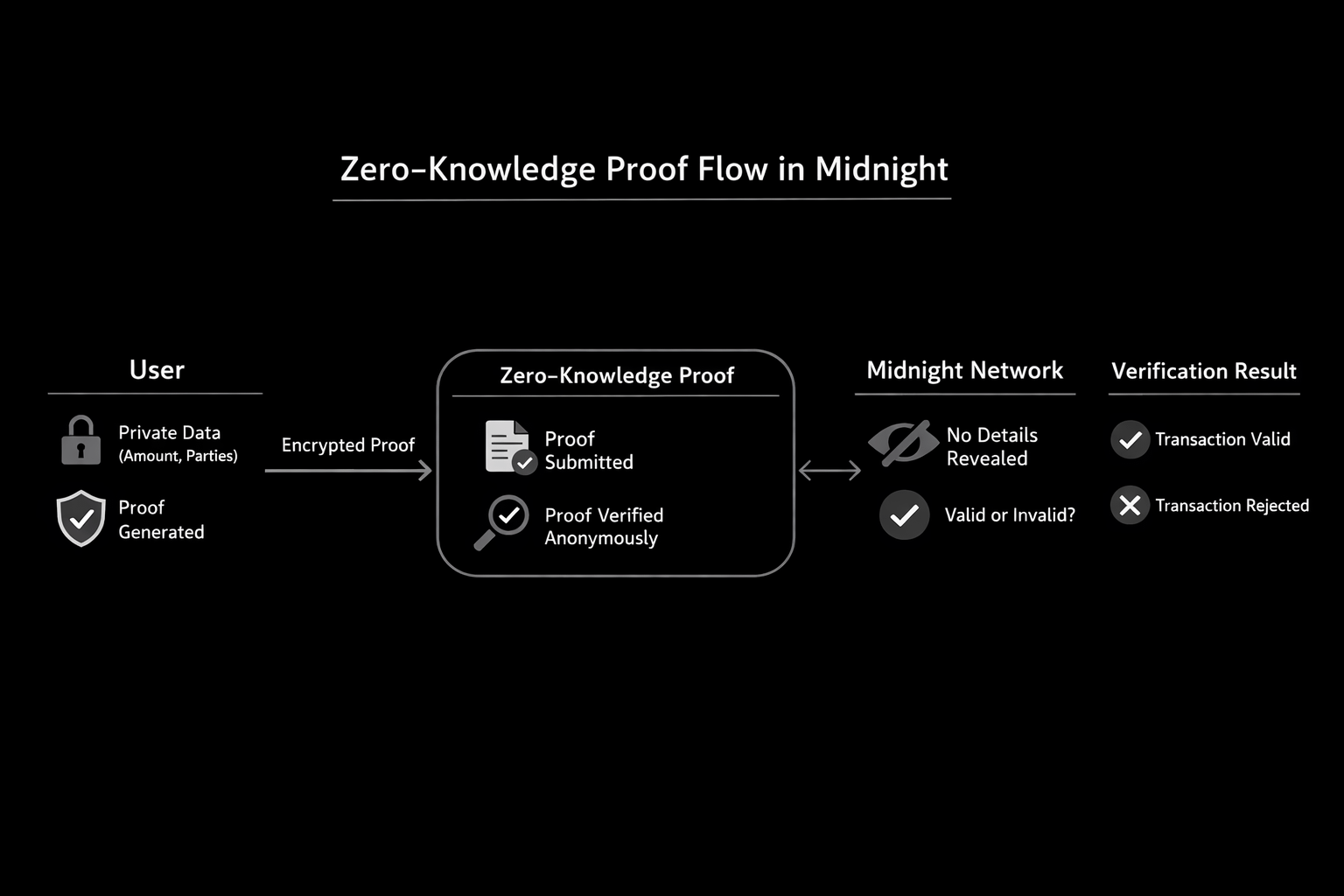
The accountability aspect comes from the way zero-knowledge proofs are structured. They’re not just cryptographic magic; they include verifiable constraints that prevent cheating. For example, if someone tried to submit a fraudulent transaction, the proof wouldn’t validate. This creates a subtle balance: the system preserves privacy, yet malicious behavior can still be detected. Think of it as a locked envelope with a certified stamp inside — anyone can trust the stamp without opening the envelope. It’s a different flavor of trust, one that doesn’t rely on complete transparency.
Real-world behavior illustrates some of the tension in this approach. Consider a decentralized identity verification system. A user wants to prove they are over 18 without revealing their full birth date or identity. Midnight’s zero-knowledge proofs can handle this neatly. The verifier receives confirmation that the condition is met without ever seeing the user’s actual data. But this also introduces complexity. If the proof system is misconfigured or misunderstood, it can produce valid-looking proofs that are subtly flawed, potentially allowing misuse. This is a limitation that cannot be ignored: privacy without accountability is meaningless, but accountability without careful design can undermine privacy.
Another interesting scenario is supply chain auditing. Imagine a manufacturer needing to prove compliance with environmental standards while keeping supplier costs confidential. On Midnight, they can submit encrypted proofs that meet the auditor’s requirements without exposing every transaction in the chain. This is particularly useful when companies want to demonstrate responsibility to regulators or customers but fear revealing competitive information. However, the tradeoff is computational load. Generating and verifying zero-knowledge proofs is not trivial. It can slow down processes, require additional technical expertise, and, in some cases, increase operational costs.
One nuance of Midnight’s system is that privacy is selective, not absolute. Users or systems can choose which data to encrypt and which to share. This allows flexibility but requires careful governance. If a participant shares too much publicly, the privacy benefits of the network are weakened. Conversely, if everyone encrypts everything, the system may become opaque even to legitimate stakeholders, making coordination difficult. This tension is an ongoing challenge for any privacy-focused blockchain, and Midnight handles it with configurable layers that let participants calibrate privacy to context.
It’s also worth noting that Midnight’s approach reshapes how audits and disputes function. Traditional auditing often relies on direct access to raw data. With zero-knowledge proofs, auditors receive proofs instead of raw data. They must trust that the proofs accurately represent reality. While cryptographically sound, this introduces a layer of abstraction that some auditors or regulators may find uncomfortable. It’s an unusual shift: trust moves from transparency of data to confidence in cryptography.
What happens when things go wrong? Say a user accidentally submits incorrect information in a proof, or a technical bug occurs in the proof verification system. Midnight does not automatically expose errors, so detecting mistakes can be harder than on transparent chains. There’s a subtle tradeoff between privacy and diagnosability. Errors that would be obvious on a public ledger might go unnoticed for longer, potentially causing disputes or inefficiencies. Developers and users need to remain vigilant, but the promise of privacy makes that vigilance worthwhile for many applications.
Even when these limitations, Midnight demonstrates a fascinating balance. It shows that privacy and accountability don’t have to be mutually exclusive, but the balance is delicate. Users gain control over what they reveal, systems can enforce fairness and validity, and external observers are kept out of sensitive data flows. Yet every added layer of privacy brings operational complexity and potential risks that must be managed. The network is a live experiment in cryptography applied to real-world coordination, and watching it in action raises questions about how far privacy can go without undermining the very accountability it seeks to preserve.
Midnight’s approach also invites broader reflection: as more platforms explore privacy-preserving technologies, society will need to consider how much trust we are willing to place in cryptography versus transparency. Users gain freedom and security, but they also accept that some forms of oversight may no longer be straightforward. The tension is subtle, but it’s there in every transaction, every proof, and every layer of the network. Watching these dynamics unfold is almost like observing a new type of social contract — one written not in legal text but in cryptographic logic.
It’s clear that Midnight doesn’t eliminate the tradeoffs of privacy; it reframes them. The system asks participants to engage with complexity and to think critically about what it means to keep data safe while remaining accountable. That balance is not permanent, and it will shift as the network grows, as applications diversify, and as the limits of zero-knowledge proofs are tested in practice. For anyone curious about privacy in blockchain, Midnight offers a hands-on glimpse of both the potential and the subtle tensions involved.